what’s trending
Editor's Pick
Latest Articles
Have you ever wondered where the technology in your gaming PC or smartphone comes from? While we often focus on the latest consumer gadgets, many core principles that contribute to our [...]
Research-based methodologies for successful data migration in complex enterprise environments SAP S/4HANA migrations represent critical technological transitions for enterprise organizations, with financial implications ranging from $250,000 for mid-market companies to $84 [...]
You've activated your VPN, but how can you be certain it’s truly protecting you? A simple “connected” status offers a false sense of security and doesn't guarantee your privacy or unlock [...]
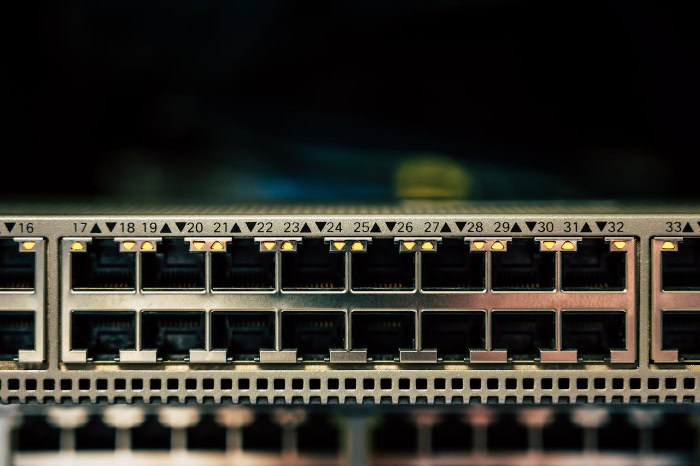
Diagnosing elusive network problems and detecting hidden security threats often requires a direct, packet-level view of network traffic. Port mirroring, a function built into modern switches, provides precisely this capability by [...]
Criminals can turn an ATM into a personal cash dispenser, bypassing card security entirely to drain its internal vaults. This type of attack, known as ATM jackpotting, represents a direct assault [...]
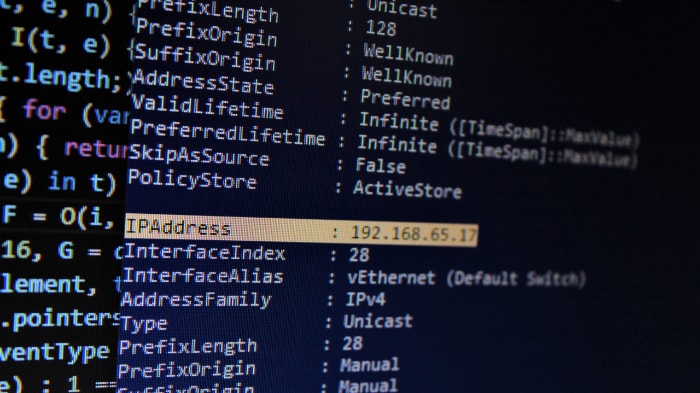
Every device on a network needs a unique address to communicate, but the method used to assign that address is a critical decision. Networks provide these identifiers in one of two [...]