Can Website Owners See Who Visits? How to Block Trackers

Clicking a web link triggers an immediate, invisible data exchange between your device and the host server. Privacy-conscious users frequently worry about who is watching them online, while administrators constantly seek better ways to monitor their site traffic.
The reality of internet tracking falls strictly between these competing interests. By default, website owners cannot see your name, home address, or exact identity.
They can, however, collect highly detailed technical data and behavioral patterns the moment you load their page. Separating personally identifiable information from your anonymous digital footprint reveals exactly what happens behind the screen.
Analyzing modern behavioral tracking methods alongside available user privacy controls exposes how much data you actually leave behind and how you can limit what others collect.
Key Takeaways
- Website owners cannot see your personal email, name, or exact street address just from you visiting their page.
- Basic analytics reveal broad technical details, including your device type, operating system, and general geographic region.
- Behavioral tracking software monitors exactly how you interact with a page, recording elements like clicks and scroll depth.
- Your anonymous identity only becomes known when you explicitly submit information through forms, checkout pages, or account logins.
- You can actively manage your privacy by using trusted virtual private networks, privacy-first browsers, and powerful content blockers.
The Limits of Web Tracking and What Owners Cannot See
A common fear among internet users is that loading a webpage instantly hands over their identity to a total stranger. Fortunately, default web browsing operates under strict technical limitations.
While administrators possess access to broad analytics, specific security barriers prevent them from peering directly into your private life.
Personally Identifiable Information
The most common misconception about online tracking involves the automatic sharing of highly sensitive details. Simply visiting a website does not reveal your name, exact home address, phone number, or personal email address.
A site owner cannot look at their traffic logs and see that a specific individual from a specific street address just read their blog post. By default, your actual human identity remains entirely separated from your browsing activity.
The Browser Barrier
Your web browser acts as a secure shield between the sites you visit and the device you use. Modern browsers restrict web pages from reaching outside their designated sandbox.
This security protocol means a website cannot access local files stored on your hard drive, read your private system data, or download your personal contact lists. The data exchange is strictly limited to the information required to render the webpage correctly.
Aggregate Data Versus Individual Profiles
Most standard analytics platforms group visitors into broad macro-level numbers and trends. A platform like basic Google Analytics is designed to show an administrator that five hundred people visited their homepage on a Tuesday, not to identify specific human beings.
Owners see generalized demographic estimates and traffic spikes rather than individual profiles. This aggregation protects individual privacy while still providing businesses with the statistical data they need to operate.
The Digital Footprint Collected Automatically

Even though your name remains hidden, your computer and internet connection still broadcast a wealth of technical details the moment a page loads. This background data helps servers deliver content efficiently while giving administrators a clear picture of their audience demographics.
Every visitor leaves behind a digital footprint composed of network and hardware information.
IP Addresses and Geolocation
Internet protocols require an IP address to route data back and forth between a server and a user. Exposing this IP address is mandatory for the internet to function, but it also reveals location data to the website owner.
An IP address shows the visitor’s city, general region, and internet service provider. It is important to note that an IP address points to a general geographical area rather than a specific house or exact street location.
Device and System Information
Websites automatically collect hardware and software details to optimize how their pages display. An owner can see your screen resolution, the operating system running on your device, and your specific browser version.
They also see the distinction between mobile and desktop users. Knowing if visitors use an iPhone running iOS or a desktop running Windows helps developers design better interfaces.
Browser Fingerprinting
While an IP address might change, websites often use browser fingerprinting to identify a returning user. This technique looks at your specific combination of browser type, installed version, language settings, timezone, and active plugins.
Because the exact combination of these factors is often highly unique to your specific device, a website can recognize your footprint even if you clear your cookies or change networks.
Referral Sources
Website owners heavily monitor the exact origin of their traffic. Referral tracking reveals exactly where a user was immediately before landing on the site.
An administrator can see if you clicked a link from a specific search engine, followed a post on a social media platform, or arrived via a hyperlink on an external blog. This data shows businesses which marketing channels actively drive traffic to their pages.
Observing On-Site Behavior and Monitoring Actions
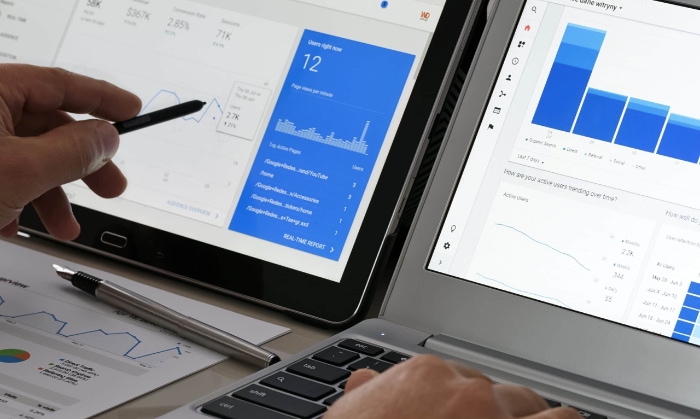
Once you land on a webpage, the focus shifts from where you came from to what you do next. Administrators utilize various software tools to monitor how visitors interact with their content in real time.
This observational data highlights which parts of a site perform well and which elements frustrate users.
Page Metrics and Engagement
Traffic analysis involves tracking a visitor’s path through the site. Site owners record the time spent on specific pages, overall navigation paths, and bounce rates.
A bounce occurs when a user visits a single page and leaves without interacting further. By analyzing these metrics, administrators determine if their content successfully holds a reader’s attention or if confusing layouts drive people away.
Cookies and Session Memory
First-party cookies serve as a short-term memory for a website. These small text files allow a site to remember a user across multiple visits and page reloads. Cookies are responsible for saving language preferences, keeping a user logged in, and ensuring items remain in a digital shopping cart while the user continues browsing.
Without session memory, the website would treat every single page click as a brand new visit from a stranger.
Visual Tracking Technologies
Beyond standard numerical data, many sites employ specialized visual tracking software to record user interactions. Heatmaps and scroll maps aggregate mouse movements, showing owners exactly where users click most often and how far down a page they scroll.
More advanced session replay tools allow an administrator to view a visual playback of a user’s mouse movements and clicks, providing a literal recording of how someone navigated the interface.
Conversion Monitoring
Ultimately, site owners want to measure specific, quantifiable actions known as conversions. Conversion monitoring tracks highly specific events, such as a user downloading a PDF, submitting a contact form, playing an embedded video, or abandoning a full shopping cart.
Tracking these specific actions allows businesses to calculate their success rates and identify exact drop-off points in their sales or registration processes.
Bridging the Gap and Identifying Anonymous Visitors
While default browsing keeps your identity hidden, specific actions quickly bridge the gap between an anonymous technical footprint and a known human being. Website owners employ multiple methods to connect browsing behavior with actual identities or specific organizations.
Once this connection occurs, all prior anonymous interactions are often linked directly to a verified user profile.
Voluntary Data Submission
The most direct way a website learns who you are is simply because you told them. When you fill out a contact form, subscribe to an email newsletter, or complete a checkout process, you explicitly hand over your personal details.
The analytics software operating in the background immediately links your previously anonymous session data to the name and email address you just provided. Everything you clicked on before hitting the submit button becomes part of your identified user file.
Account Creation and Logins
Authenticated user accounts provide administrators with a powerful method to track behavior over long periods. When you create an account and log in, the website assigns a persistent identifier to your profile.
This mechanism allows the owner to track your activity across different devices. If you browse an online store on your phone during your morning commute and later log in from your home computer to finish the purchase, the system recognizes you as the exact same person.
Business-to-Business IP Reversal
Websites operating in the business-to-business sector frequently use specialized lead-generation tools to uncover corporate visitors. While standard analytics only show general internet service providers, these advanced tools match visiting IP addresses against databases of known corporate networks.
This process reveals exactly which company visited the site. Even if the specific employee sitting at the keyboard remains anonymous, the site owner knows that someone from a specific corporation spent thirty minutes reading their pricing page.
Cross-Site Tracking and Retargeting
Third-party advertising networks completely change how behavior is tracked across the broader internet. Many websites install tracking scripts from major platforms like Meta or Google to monitor their audience.
These scripts connect your activity on one independent website directly to your authenticated social media profiles or search engine accounts. This cross-site tracking allows businesses to serve you highly targeted advertisements on different platforms based on the exact products you viewed hours earlier on an unrelated page.
Balancing Utility and Privacy Controls

As tracking technologies become more advanced, the tension between data collection and user privacy requires careful management. Both internet users and website owners have access to specific controls that dictate how information is gathered, shared, and stored.
These mechanisms ensure a functional internet while providing necessary boundaries for personal privacy.
User-Side Privacy Tools
Everyday internet users have access to a variety of software solutions to limit what website owners see. Virtual Private Networks mask your true IP address by routing traffic through secure servers elsewhere in the world. This encryption does more than just hide your location from web administrators; it actively stops your own Internet Service Provider from logging your browsing history, selling your data to marketers, or throttling your bandwidth based on your streaming habits.
Beyond stopping home network surveillance, a VPN serves as an essential safety layer when utilizing unsecured public Wi-Fi at airports, cafes, or hotels, where malicious owners or nearby hackers can easily intercept unencrypted traffic. For reliable protection, premium options like NordVPN offer robust security without tracking your activity.
You should absolutely avoid free VPN services. Operating global servers is incredibly expensive, and free providers frequently cover their costs by secretly logging and selling your browsing data to advertisers, entirely defeating the purpose of a privacy tool.
To stop invisible background scripts, browser extensions offer a strong line of defense. Powerful content blockers like uBlock Origin intercept network requests to known tracking domains, effectively preventing analytics platforms from recording your behavior.
Alternatively, many users simply switch to privacy-first browsers. Brave automatically blocks third-party ads and trackers right out of the box without needing extra plugins. For maximum anonymity, the Tor browser bounces traffic through a decentralized network of encrypted relays, making it nearly impossible to trace an IP address, though it significantly reduces connection speeds.
Data Protection Regulations
Governments around the world have implemented strict legal frameworks to govern how website administrators handle data. Regulations like the General Data Protection Regulation in Europe and the California Consumer Privacy Act explicitly define what information owners can legally collect.
These laws require businesses to securely store user data and strictly limit how long they can retain it. Violating these frameworks can result in massive financial penalties, forcing website owners to prioritize data security.
Consent Management
Because of modern privacy laws, website owners must actively secure permission before deploying non-essential tracking technologies. This requirement is the reason transparent cookie banners appear on almost every webpage today.
Administrators must clearly define their data usage policies and explain exactly what information they gather. Most importantly, they must provide visitors with an accessible method to opt out of non-essential tracking, ensuring that users retain the final say over their personal data.
Conclusion
The internet operates on a constant exchange of information, but a clear boundary exists between anonymous data gathering and personal identification. Unless you explicitly share your details through forms or account logins, administrators cannot see your name or read your private files.
They simply collect technical footprints and behavioral statistics to understand how their pages perform and where their traffic originates. Ultimately, online tracking represents an ongoing compromise.
Businesses require robust analytics to optimize their services and survive in a competitive market, while individuals deserve the right to protect their digital privacy. By utilizing the right tools and understanding exactly what data you broadcast, you can confidently browse the web without sacrificing your personal boundaries.
Frequently Asked Questions
Can a website owner see my exact address?
No, website owners cannot see your exact street address. They can only see the IP address provided by your internet service provider. This technical data reveals your general city or geographic region, but it never points directly to your specific house or apartment.
Does incognito mode hide my IP address?
Incognito mode does not hide your IP address from the websites you visit. It only stops your own device from saving your browsing history and deletes local cookies. To actually mask your location and IP address from site administrators, you must use a trusted virtual private network.
Can websites see what other tabs I have open?
Modern web browsers run each tab in a secure, isolated environment. A website cannot see the contents or URLs of other tabs you currently have open. However, third-party advertising scripts might track your general browsing habits across multiple sites if you lack content blockers.
How do websites know my name without me logging in?
Websites do not know your name unless you provide it. If a site greets you by name, it is because you previously created an account, filled out a form, or allowed third-party cookies to link your current session to a known profile from another platform.
Is it legal for websites to track my behavior?
Yes, tracking user behavior is entirely legal, provided the website complies with regional data protection laws. Regulations like the GDPR require businesses to clearly state their data collection policies and offer visitors a transparent way to opt out of non-essential tracking technologies.


