Is qBittorrent Safe to Use? Everything You Need to Know

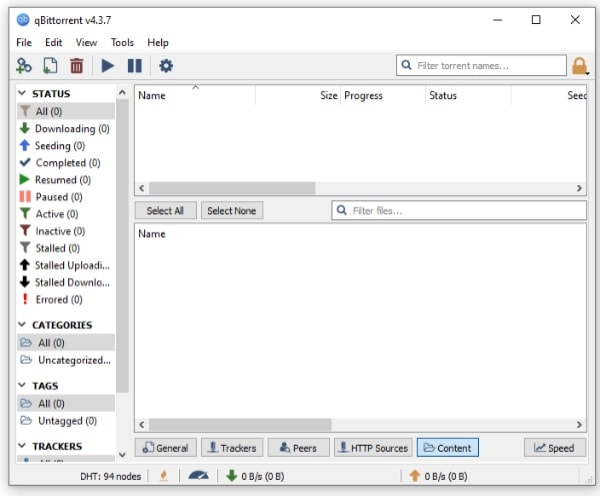
Choosing a torrent client often feels like a gamble between performance and security. Most users eventually find qBittorrent, a free and open-source program that promises a fast experience without the invasive advertisements found in rival apps.
Despite its popularity, the same concern remains for every new download: is this software actually a threat to your computer?
The short answer is that qBittorrent is widely considered the safest and most reliable client available today. It is clean, transparent, and built by a community of volunteers rather than a corporation seeking your data.
That said, even the best tool can become dangerous if used improperly. True security depends on using official download sources and maintaining strict habits while interacting with the peer-to-peer network.
Key Takeaways
- qBittorrent is free, open source, and contains no advertisements or bundled malware.
- The software is safe, but it cannot protect you from viruses hidden inside files you download.
- Binding the client to your VPN interface is the most effective way to prevent IP address leaks.
- Always use the official website for downloads to avoid malicious versions of the installer.
- Security software often flags the program as a false positive due to the nature of the protocol.
The Security Foundation of qBittorrent
The software itself is built on a philosophy of transparency and user privacy. Unlike many commercial applications that prioritize revenue, qBittorrent is a community driven project that focuses entirely on providing a clean, functional utility for the BitTorrent protocol.
Its safety is a direct result of how the software is developed and maintained by its volunteer contributors.
The Transparency of Open Source Code
One of the most significant security advantages of qBittorrent is its open source nature. The entire source code is available for public inspection, which allows security researchers and developers from around the world to audit the software.
This level of scrutiny makes it nearly impossible for a developer to hide malicious scripts, backdoors, or spyware within the program. If a vulnerability or a suspicious piece of code were introduced, the global community would likely identify and report it almost immediately.
Freedom from Malvertising and Bloatware
Many popular torrent clients, such as uTorrent, have faced criticism for including intrusive advertisements or “bloatware” in their installers. These third party programs are often bundled to generate profit, but they can compromise system performance and user privacy.
In some cases, these ads have been used to distribute malware, a tactic known as malvertising. qBittorrent avoids these risks entirely.
It does not contain any advertisements, and the installer is free from hidden software or unwanted toolbars.
A Non-Profit Model Without Commercial Conflict
Because qBittorrent is a volunteer project that relies on donations rather than corporate funding, there is no financial incentive to exploit the user base. Commercial software companies often face pressure to monetize their users through data collection or by including crypto miners in their code.
qBittorrent has no shareholders or profit targets to meet; its only goal is to provide a high quality, neutral tool for file sharing. This lack of commercial conflict ensures that user security is never traded for a profit margin.
Antivirus Warnings and False Positives

Even though qBittorrent is safe, users often encounter scary warnings from security software when they try to install or run it. These alerts can be misleading for those who are not familiar with how antivirus programs categorize certain types of software.
The Potentially Unwanted Application Label
Windows Defender and other major antivirus suites frequently flag torrent clients as a Potentially Unwanted Application, or PUA. This classification does not necessarily mean the software is a virus.
Instead, it serves as a warning that the software can be used to download high risk content or that it might consume significant network bandwidth. Security companies often err on the side of caution by flagging all peer to peer tools, regardless of their actual safety, because of the behavior of the protocol they use.
The Dangers of Unofficial Downloads
A major security risk involves where the software is sourced. Because qBittorrent is popular, malicious actors often create fake websites or “cracked” versions of the software that contain actual trojans or ransomware.
There is no such thing as a “Pro” or “Premium” version of qBittorrent. Any site claiming to offer a paid or enhanced version is distributing malware.
To stay safe, users must only obtain the software from its official repository or the official project website.
Verifying the Installer Integrity
For users who want absolute certainty that their download has not been tampered with, verifying the installer is a professional standard practice. The developers provide SHA-256 checksums and PGP signatures for every release.
By comparing the checksum of the downloaded file with the one listed on the official site, a user can confirm that the file is an exact, untampered copy of the original. This process ensures that no malicious code was injected into the installer by a third party during the download process.
Distinguishing Software Safety from Protocol Risks
It is vital to understand that a safe application does not make every action performed within that application safe. There is a clear distinction between the integrity of qBittorrent as a program and the risks inherent to the BitTorrent protocol itself.
A secure tool can still be used to engage in risky activities if the user is not careful.
Safe Tools vs Dangerous Content
qBittorrent functions like a browser or a file explorer; it is a vehicle for moving data. While the software is clean and free of viruses, it cannot prevent you from downloading a malicious file from the internet.
If a user downloads a torrent that contains a virus, the client will facilitate the transfer just as it would for a safe file. The software does not have a built-in antivirus to scan the contents of every download, so the responsibility for vetting files remains with the user.
Exposure of Your IP Address
The BitTorrent protocol relies on a peer to peer network where users upload and download data from each other simultaneously. To facilitate this, your IP address must be broadcast to every other user in the “swarm” who is sharing the same file.
This is not a flaw in qBittorrent, but rather a fundamental requirement of how the technology works. Without additional protection, your location and service provider information are visible to anyone else connected to the same torrent.
Legal Realities of Torrenting
The software is entirely legal to own and use for many legitimate purposes, such as downloading Linux distributions or public domain media. However, using the software to download copyrighted material without permission carries significant legal risks.
Many internet service providers monitor for this activity, and copyright holders often join swarms to collect IP addresses for legal action. qBittorrent provides the technology for file sharing, but it does not offer legal immunity or inherent anonymity for the actions a user chooses to take.
Essential Safety Features and Configurations

While the default settings of qBittorrent are functional, the client includes several advanced options that can significantly increase your security. Proper configuration allows you to seal potential data leaks and ensure that your activity remains as private as possible.
By taking the time to adjust these settings, you turn the software from a simple downloader into a hardened privacy tool.
The Security Benefits of VPN Binding
Many users rely on a VPN kill switch to protect their identity, but this method is often unreliable because it depends on software detecting a connection failure. qBittorrent offers a superior alternative known as network interface binding.
By going into the advanced settings, you can instruct the client to communicate only through your VPN network interface. If the VPN connection drops for even a millisecond, qBittorrent will find itself without a valid network path and will instantly stop all traffic.
This creates a leak proof environment that ensures your real IP address is never exposed to the peer swarm.
Forcing Encrypted Connections
Internet Service Providers often use a technique called packet inspection to identify and slow down torrent traffic. To counter this, qBittorrent allows you to manage encryption protocols for every connection.
By setting the encryption mode to “Require encryption,” you force the client to ignore any peers that do not support an encrypted link. This hides the nature of your traffic from your ISP and adds a layer of protection against local network snooping.
It is important to note that this may slightly reduce the number of available peers, but the privacy gain is worth the trade.
Understanding Anonymous Mode
qBittorrent includes a specific setting called Anonymous Mode, which is often misunderstood. When enabled, this feature strips away identifiable metadata from your connection, such as your computer’s name and the specific version of the software you are using.
While this helps minimize your digital footprint, it is not a replacement for a VPN. Your IP address is still visible to the peers you are connecting with because the protocol requires it.
Anonymous Mode is best used as a secondary layer of defense alongside a properly configured VPN.
Managing DHT and PEX for Privacy
Distributed Hash Table (DHT) and Peer Exchange (PEX) are features that help you find more peers without relying on a central tracker. While these are useful for public torrents, they can compromise your privacy when using private trackers.
Most private communities require you to disable these features to ensure that the file sharing remains restricted to authorized members. Disabling DHT and PEX prevents your client from reaching out to the wider public internet, keeping your activity contained within a trusted group of users.
Best Practices for Secure Torrenting

Beyond configuring the software correctly, your personal habits play a massive role in maintaining a clean system. The most advanced security settings in the world cannot protect you if you intentionally run a malicious file or ignore software updates.
Adopting a cautious mindset is the most effective way to avoid the common pitfalls associated with peer to peer sharing.
Utilizing Trusted Content Sources
The easiest way to avoid malware is to be selective about where you find your torrents. Private trackers are often considered the gold standard for safety because they require an invitation and maintain strict quality control.
If you prefer public sites, look for those with active communities and comment sections. Reputable sites often designate certain uploaders as “trusted” or “verified” based on their history of providing clean, high quality files.
Always check the comments for reports of viruses or poor file quality before starting a download.
Vetting Files Before Execution
A common trick used by malicious actors is to disguise an executable script as a media file. For example, a file might be named “Movie.mp4.exe,” but since Windows often hides file extensions by default, a user might only see “Movie.mp4” and assume it is safe.
Before opening any file, check its properties to confirm the actual file type. Be extremely wary of any download that includes .exe, .vbs, or .bat files unless you are specifically downloading software from a source you trust implicitly.
Maintaining Software Updates
Software developers regularly release updates to patch security vulnerabilities that could be exploited by hackers. Using an outdated version of qBittorrent leaves you exposed to known bugs that have already been fixed in newer releases.
You should check for updates frequently or enable the built in notification feature to ensure you are always running the most secure version of the client. Staying current is a simple but vital part of maintaining a healthy and secure digital environment.
Disabling Tracker Favicons
A specific issue that has recently caused confusion involves tracker favicons, which are the small icons that appear next to a torrent’s name. Some antivirus programs flag the temporary folder where these icons are stored as a potential trojan threat.
While these are usually false positives, you can eliminate the risk and the annoying notifications by disabling the “Use icons from trackers” option in the settings. This prevents the software from downloading these small images, keeping your temporary folders clean and avoiding unnecessary alerts from your security software.
Conclusion
qBittorrent remains a safe and powerful tool for anyone needing a reliable BitTorrent client. Its open source development ensures that the code remains transparent and free from the profit driven motives that affect other software.
By removing advertisements and malicious bloatware, it provides a streamlined experience focused entirely on performance and privacy.
Ultimate safety is a shared responsibility between the software and the user. While the client provides the necessary tools for protection, you must implement configurations like VPN binding and practice caution when selecting files.
With a reputable VPN and a bit of common sense, qBittorrent stands as the gold standard for secure file sharing.
Frequently Asked Questions
Is qBittorrent better than uTorrent?
Yes, qBittorrent is generally preferred because it is open source and contains no advertisements or bundled software. While uTorrent is a commercial product that has historically included bloatware, qBittorrent remains a community project funded by donations. This makes it a cleaner and more privacy focused option for most users.
Does qBittorrent hide my IP address?
No, the software does not hide your IP address on its own. Because of how peer to peer networking functions, your IP is visible to others in the swarm to allow data exchange. To mask your location and identity, you must use a reliable VPN and bind it to the client.
Why does my antivirus block qBittorrent?
Antivirus programs often flag torrent clients as Potentially Unwanted Applications because they can be used to download risky content. This is usually a false positive designed to protect less experienced users. As long as you download the installer from the official website, the software itself is safe to run.
Is torrenting legal with qBittorrent?
The software is a legal tool for sharing files, such as open source software or public domain media. However, using it to download copyrighted material without permission is illegal in many countries. The legal safety of your activity depends entirely on the specific files you choose to share.
Can qBittorrent infect my computer with a virus?
The application is clean and does not contain viruses; however, it cannot scan the files you download. If you download an infected file from an untrusted source, your computer can still become compromised. You must use common sense and verify every file you download before opening it.


