What Is a MAC Address? How Devices Communicate

Before a single message, video, or webpage can load on a screen, networks must know exactly who is asking for the data. A Media Access Control (MAC) address provides this unique physical identity.
It acts as a permanent hardware fingerprint assigned directly to a device's network chip by the manufacturer.
To make sense of these connections, you will learn the precise anatomy of this twelve-character code and how it differs from a standard IP address. Clear instructions will help you easily locate the hardware address on a smartphone, computer, or smart home gadget.
Beyond finding the address, you will see practical networking uses like access control and device management. Lastly, new privacy protocols demonstrate how modern operating systems protect user identities from location tracking on public Wi-Fi networks.
The Anatomy and Format of a MAC Address
Every piece of hardware that connects to a network possesses a distinct physical signature. A MAC address might look like a random jumble of letters and numbers, but it follows a strict organizational standard.
Breaking down this code reveals specific details about the device's origin and identity.
The Hexadecimal Structure
A standard MAC address consists of twelve alphanumeric characters. These characters operate on a hexadecimal system, meaning they use the numbers zero through nine and the letters A through F.
To make the sequence readable for humans, the twelve characters are grouped into pairs, called octets. Network interfaces usually display these pairs separated by colons or hyphens, such as 00:1A:2B:3C:4D:5E.
Organizationally Unique Identifier
The first half of the MAC address serves a very specific purpose. These first three octets form the Organizationally Unique Identifier, or OUI.
The Institute of Electrical and Electronics Engineers assigns these unique prefixes directly to hardware manufacturers. By looking up the OUI, network administrators can instantly tell if a device was manufactured by a major tech company like Apple, Intel, or Samsung.
Network Interface Controller Specifics
The second half of the address functions differently. The manufacturer assigns the last three octets to the specific Network Interface Controller inside the device.
This portion acts as a unique serial number for that exact network chip. Even if a factory produces thousands of identical network cards on the same day, every single one receives a unique sequence for these final six characters.
Physical Versus Logical Addresses
In networking terminology, a MAC address functions as a physical address rather than a logical one. During the manufacturing process, the complete twelve-character code is permanently “burned in” to the network hardware's read-only memory.
Unlike software-based addresses that can change based on network configurations, the true hardware MAC address remains a permanent fixture of the physical network chip itself.
MAC Address Versus IP Address
Devices rely on two distinct types of addresses to communicate effectively. While people often confuse MAC addresses with IP addresses, the two systems serve completely different functions in routing network traffic.
They work together to ensure data reaches the correct destination.
The Postal Analogy
The easiest way to grasp this relationship is through a postal analogy. An IP address acts much like the mailing address of a house.
It dictates the general geographic location and guides the postal worker to the correct neighborhood and street. The MAC address represents the actual person living inside that house, similar to a physical identity or a Social Security Number.
The IP address gets the data to the right building, while the MAC address ensures the information goes into the exact hands of the intended recipient.
Network Layers Explained
These addresses operate on different levels of network communication. MAC addresses function on the local level, known as the Data Link Layer or Layer 2 in networking models.
They handle the movement of data between devices connected to the same home or office network, such as a laptop communicating directly with a Wi-Fi router. IP addresses operate on a broader scale at the Network Layer, or Layer 3. They manage the complex routing required to send data across the global internet.
Permanence and Mobility
Another major distinction lies in how these addresses handle change. A physical MAC address remains static.
The hardware retains the same identity regardless of where the device travels. Conversely, IP addresses are dynamic and change constantly.
When a smartphone moves from a home Wi-Fi network to a local coffee shop connection, the device receives a brand new IP address from the new network, while its underlying hardware MAC address stays exactly the same.
Locating Your Device's MAC Address

Finding the physical hardware address requires searching through a few basic system menus or command prompts. The exact process varies depending on the operating system or hardware type.
Most interfaces label this code clearly as the Physical Address, Wi-Fi Address, or simply the MAC.
Finding the Address on Windows
On a Windows computer, users have two primary methods to locate this information. The fastest route involves opening the Command Prompt application and typing ipconfig /all before pressing Enter.
The system will display a list of network adapters, and the physical address will appear next to the active connection. Alternatively, users can open the graphical Network and Internet settings menu, select their active Wi-Fi or Ethernet connection, and view the hardware properties to find the physical address listed.
Locating the Hardware Address on macOS
Apple computers display their network hardware identifiers within the main system preferences. Users must open System Settings and select the Network menu.
Clicking on the active connection, whether Wi-Fi or Ethernet, reveals a details or advanced button. Inside this advanced menu, the hardware tab clearly displays the twelve-character MAC address assigned to that specific Apple network interface.
Checking Mobile Devices
Smartphones also provide easy access to these network identifiers. On an iPhone or iPad, the identifier is labeled as a Wi-Fi Address and can be found by opening the Settings app, tapping General, and selecting the About menu.
Android devices follow a very similar path. Users can open their Settings app, scroll down to About Phone, and look for the network information or status menu to view the device Wi-Fi MAC address.
Smart Home and Internet of Things Devices
Locating network identifiers on devices without traditional screens requires a different approach. Smart TVs, gaming consoles, and smart plugs often have their hardware addresses printed on a physical sticker located on the back or bottom of the device.
If the physical label is missing or unreadable, the most reliable method involves logging into the home router's administrative portal. The router maintains a list of all connected clients, displaying the assigned IP address alongside the physical MAC address for every active smart home gadget.
Network Management and Practical Uses

Beyond simple device identification, network administrators utilize physical hardware codes to build organized and secure systems. Routers rely on these unique identifiers to process requests, restrict access, and assign consistent network pathways for every connected machine.
Device Identification
Network managers use MAC addresses to accurately map exactly which devices operate on a local network. Because the first half of the code reveals the hardware manufacturer, administrators can quickly identify the type of equipment requesting access.
This visibility makes it easy to categorize connected hardware, allowing network managers to separate corporate laptops from unauthorized personal smartphones or smart home gadgets.
MAC Filtering
Administrators can configure Wi-Fi routers to use physical addresses as an active security checkpoint. Through a process called MAC filtering, routers maintain specific lists to control network access strictly.
An allowlist, often called a whitelist, permits only recognized devices to join the network. Conversely, a blocklist specifically prevents unwanted hardware from gaining access.
While determined intruders can eventually bypass this method, it effectively stops casual unauthorized users from connecting to private Wi-Fi routers.
Static IP Assignments
Many smart devices operate best when they maintain a predictable location on the local network. Gadgets like network printers, media servers, or security cameras need the exact same local IP address every time they boot up so other computers can find them reliably.
Routers achieve this stability through DHCP reservations. The router links a specific local IP address directly to the device's unique MAC address.
Whenever that specific network interface powers on and connects, the router immediately recognizes it and hands out the reserved IP address.
Privacy, Security, and MAC Randomization

While hardware identifiers provide structure for local networks, their permanent nature creates significant privacy concerns in public spaces. Because mobile devices broadcast these codes openly while searching for connections, modern technology companies have implemented software changes to protect user locations from passive surveillance.
The Risk of Physical Tracking
Smartphones and laptops constantly send out probe requests to find nearby Wi-Fi networks. During this routine background process, devices traditionally broadcast their permanent hardware MAC address.
Retailers, advertisers, and malicious actors can set up passive sensors in public spaces, such as shopping malls or transit stations, to capture these broadcasts. By logging the unique identifier at various locations, observers can track a person's movements, monitor their daily habits, and build a detailed profile of their physical location without the user ever actually joining a Wi-Fi network.
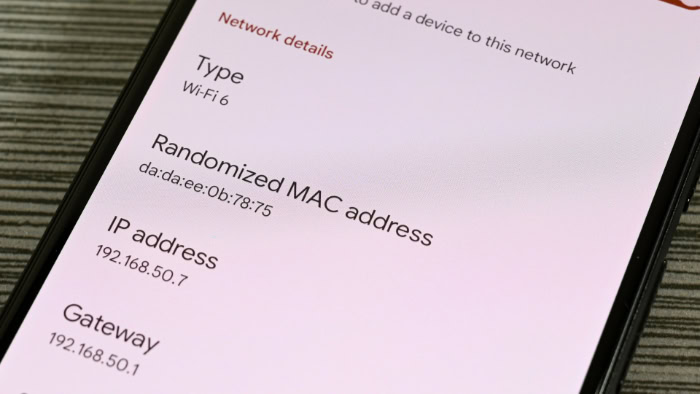
MAC Randomization Explained
Software developers recognized this tracking vulnerability and introduced MAC randomization to protect user privacy. Modern operating systems across Apple, Android, and Windows software no longer broadcast their true hardware addresses while scanning for public networks.
Instead, the software generates a temporary, randomized MAC address for every different Wi-Fi network the device encounters. This process obscures the physical hardware identity and breaks the surveillance chain, as the device appears as a completely new and unrelated piece of hardware at each new location.
MAC Spoofing
Users also have the ability to intentionally alter their broadcasted hardware identity through a technique called MAC spoofing. By using specialized software or system commands, a person can temporarily change the MAC address their device presents to a network router.
People utilize this method for legitimate privacy protection or to test network security protocols. Additionally, spoofing allows users to bypass certain network restrictions, such as circumventing time limits on public Wi-Fi networks that track usage based on hardware addresses.
The physical chip inside the device remains completely unchanged, but the software successfully feeds the network a fabricated identity.
Conclusion
Every piece of data moving across a local network relies on a MAC address to reach its final destination. This twelve-character code serves as the fundamental building block of local communication, ensuring routers and switches direct traffic to the correct physical hardware.
While originally designed as a strict, permanent identifier burned into every network chip, the role of this address has shifted dramatically over the years. Thanks to modern software randomization and spoofing techniques, a fixed hardware signature now functions as a flexible tool, balancing efficient network management with essential personal privacy.
Frequently Asked Questions
What is the main purpose of a MAC address?
A MAC address physically identifies a specific device on a local network. It allows routers and switches to send data to the correct piece of hardware. Without this unique identifier, your local network would not know where to route incoming information.
Can two devices have the same MAC address?
Manufacturers assign a globally unique MAC address to every network controller they produce. Therefore, no two physical devices should ever share the exact same hardware code. However, users can use software tools to temporarily spoof an address, creating a duplicate on a specific network.
Does my MAC address change when I change Wi-Fi networks?
Your physical hardware address never changes, regardless of your location. However, modern smartphones and computers use software randomization to broadcast a temporary, fake address to new public networks. This process protects your privacy by preventing passive tracking across different physical locations.
Who can see my MAC address?
Only devices directly connected to your local network can see your MAC address. Your home router, network switches, and other local computers have access to this information. Websites and remote servers on the broader internet only see your public IP address.
Is it safe to share my MAC address?
Sharing your MAC address poses very little security risk over the internet, as it only functions on local networks. However, you should avoid broadcasting your true hardware address on public Wi-Fi. Malicious actors on the same local connection could potentially track your physical movements.


