What Is Torrenting? Is It Actually Illegal?
Most internet users are familiar with the standard download method where a file travels from a central server directly to a device. Torrenting completely upends this model.
It is a peer-to-peer file-sharing process based on the BitTorrent protocol that allows users to download pieces of data from one another simultaneously. This decentralized approach solves the bandwidth bottlenecks that plague traditional downloads and makes moving massive files incredibly efficient.
Despite its utility, the term often triggers confusion regarding safety and legality due to its frequent association with digital piracy.
The Architecture of Torrenting
Most internet activity relies on a straightforward relationship where a computer requests data and a server delivers it. Torrenting breaks this linear path by creating a web of connections where every participant contributes to the transfer.
This structure fundamentally changes how files move across the internet and solves many logistics problems associated with distributing large amounts of data.
Traditional Downloading (Client-Server Model)
The standard method for acquiring files on the web is the Client-Server model. When you download a photo or a document from a website, your device acts as the client.
It sends a request to a central server where that file is hosted. The server processes the request and sends the data back to you.
This works well for small files and web browsing.
However, this model has significant limitations when handling large files or heavy traffic. The central server represents a single point of failure; if it crashes or goes offline, nobody can access the content.
Furthermore, the server has a fixed amount of bandwidth. If thousands of users try to download a large file simultaneously, the server becomes overwhelmed.
This creates a bottleneck that results in slow speeds for everyone.
The Peer-to-Peer Solution
Torrenting utilizes a Peer-to-Peer (P2P) architecture to eliminate the reliance on a central server. Instead of downloading a file from one source, the BitTorrent protocol breaks the file into hundreds or thousands of tiny data chunks.
You then download these chunks from other users who already have them on their computers.
This decentralization creates a “swarm.” The swarm consists of all the computers currently sharing a specific file.
As you download chunks of data, your computer automatically begins uploading those same chunks to other users in the swarm. You are not just a recipient; you become a distributor.
The workload is spread across every user in the network rather than resting on one machine.
Efficiency at Scale
The most distinct advantage of P2P architecture is how it handles popularity. In the traditional model, high traffic slows down the download speed because the server must divide its resources among more people.
In torrenting, the opposite happens. As more people join the swarm to download a file, the speed and efficiency often increase.
Every new user brings their own bandwidth and resources to the group. Since every user contributes data while they download, a popular file with thousands of active peers will usually download much faster than a file with only a few peers.
This makes the protocol ideal for distributing massive files like high-definition video or large software packages without incurring massive server hosting costs.
Terminology and Mechanics
To participate in a swarm effectively, you need specific software and a grasp of the vocabulary used by the community. The files you interact with are often just instructions rather than the content itself.
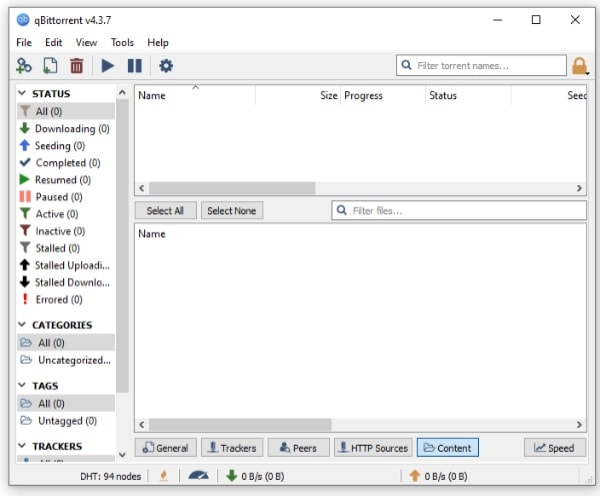
The Role of the Torrent Client
Web browsers are not designed to handle the complex connections required for P2P file sharing natively. To torrent, you must install a specific piece of software known as a torrent client.
Popular examples include qBittorrent, Transmission, or uTorrent.
The client acts as the manager for your downloads. It interprets the instruction files, finds other users who have the data you need, and manages the simultaneous upload and download connections.
It also reassembles the thousands of tiny data chunks back into a usable file once the download is complete.
Metadata and Magnet Links
You cannot download the actual content directly from a website. Instead, you download a metadata file that tells your client where to look.
Historically, this was done using a .torrent file. This small file contains information about the folder structure, file names, and integrity checks, but it contains zero actual content.
Today, most sites use Magnet Links. A magnet link contains a unique identifier code for the file.
When you click it, your client immediately opens and connects to the swarm to fetch the metadata and the content directly from other peers. This eliminates the need to download and store a .torrent file on your hard drive before starting the process.
Participants in the Network
Once you connect to a swarm, you will see various terms describing the other users in the network. Their roles are defined by how much of the file they possess.
- Seeders: These are the most important users in the swarm. A seeder has downloaded 100% of the file and keeps their client open to upload it to others. Without seeders, a torrent inevitably dies because no complete copy of the file exists.
- Leechers/Peers: These users are currently in the process of downloading the file. They do not have the complete data set yet. While they download, they also upload the parts they have already finished to other leechers.
- Trackers: A tracker is a specific type of server that helps coordinate the swarm. It does not host any files. Instead, it acts as an introduction point, sharing the IP addresses of peers so they can connect to one another.
The Legality of Torrenting
The reputation of torrenting is tied heavily to piracy, yet the technology itself remains neutral. Knowing the distinction between the tool and how it is utilized is essential for staying on the right side of the law.
The legal risks arise entirely from the copyright status of the data being shared.
The Technology vs. The Usage
The BitTorrent protocol and torrent clients are entirely legal technologies. Possessing a torrent client on your computer is no different from having a web browser, an FTP client, or an email application.
These are simply tools designed to move data efficiently from one place to another.
Problems occur only when the tool is used to transfer content without the permission of the copyright holder. The legality is determined by the content of the file, not the method of transfer.
Legitimate Use Cases
There are many scenarios where torrenting is the preferred and legal method of distribution. Because it saves bandwidth costs for the host, many organizations use it to distribute large public files.
- Open Source Software: Many Linux operating systems utilize torrents to distribute their installation images (ISOs) to millions of users without paying for massive server farms.
- Public Domain Media: Older movies and music that have entered the public domain are frequently preserved and shared via torrents legally.
- Game Updates: Large gaming companies, such as Blizzard, have utilized P2P mechanics in the background of their launchers to distribute massive game updates efficiently among their player base.
- Academic Data: Researchers often use torrents to share massive scientific datasets that would be too large to host on standard web servers.
Copyright Infringement
Torrenting becomes illegal when users download and share copyrighted material such as movies, TV shows, commercial software, or video games without authorization. In most jurisdictions, this constitutes copyright infringement.
There is a distinct legal risk with torrenting that does not exist with illicit streaming. When you stream a movie from an unauthorized site, you are generally just receiving data.
However, the nature of the BitTorrent protocol means that you are automatically uploading chunks of the file to other users while you download it. In the eyes of the law, this makes you a distributor of copyrighted material, not just a consumer.
This “distribution” aspect is what copyright trolls and legal firms target when sending settlement letters or ISP warnings.
Risks and Challenges

The decentralized nature of torrenting removes the safeguards typically provided by official servers and regulated platforms. While the technology is efficient, the environment where it operates is often unregulated and hostile.
Users who enter a swarm without precautions expose themselves to malicious software, privacy violations, and potential repercussions from their internet service provider.
Digital Hygiene and Malware
One of the most immediate dangers in the torrenting ecosystem is the prevalence of malware. Because anyone can upload a file to a public tracker, malicious actors frequently disguise viruses, ransomware, or spyware as popular content.
A file might be labeled as a newly released movie or expensive software, but the actual data inside could be a harmful executable designed to compromise your system.
“Fake” torrents are also common. These are files that look legitimate but contain nothing of value or are designed to trick users into visiting scam websites.
Maintaining strict digital hygiene is necessary. If a file size looks suspicious, such as a high-definition movie that is only a few megabytes in size, it is almost certainly a trap.
Privacy Exposure
To download a file from a swarm, your computer must directly connect to other computers. This requirement creates a significant privacy flaw.
In any active torrent, your IP address is visible to every other peer in that swarm. Your IP address is a digital fingerprint that reveals your general location and identifies your internet connection.
This transparency allows third-party agencies to monitor user activity easily. Specialized firms often join popular swarms not to download files, but to harvest the list of IP addresses participating in the transfer.
This data is logged and can be used to track downloading habits or to identify users sharing copyrighted material.
ISP Throttling and Penalties
Internet Service Providers (ISPs) generally dislike peer-to-peer traffic because it consumes massive amounts of bandwidth. To manage network congestion, many ISPs employ “throttling.”
This involves detecting P2P traffic protocols and intentionally slowing down the user’s connection speed. This can affect not just the download speed but the performance of the entire home network.
Beyond speed issues, ISPs are often the messengers for legal threats. If a copyright holder detects your IP address in a swarm sharing their content, they send a complaint to the ISP owning that address.
The ISP then forwards this warning to you. These notices can range from simple warnings to threats of service suspension or legal action depending on local laws and the severity of the offense.
Essential Safety Measures

Navigating the risks of peer-to-peer networks requires a combination of the right software and cautious behavior. By adding layers of anonymity and verifying sources, users can significantly reduce the likelihood of malware infections or privacy leaks.
Anonymity Tools and VPNs
A Virtual Private Network (VPN) is the single most effective tool for safe torrenting. A VPN reroutes your internet traffic through a secure server and encrypts it.
When you enter a swarm while using a VPN, the other peers see the IP address of the VPN server rather than your personal home address. This masks your identity from data harvesters.
Additionally, the encryption provided by a VPN prevents your ISP from seeing what you are doing. They can see that data is moving, but they cannot determine that it is P2P traffic, which helps avoid throttling.
It is critical to select a VPN that features a “Kill Switch.” This function automatically cuts your internet connection if the VPN drops for any reason, ensuring your real IP address is never accidentally exposed to the swarm.
Selecting the Right Source
Not all torrent websites are created equal. Public trackers are open to everyone and are often indexed by search engines.
These sites have the highest volume of content but also the highest risk of malware and monitoring because there is little oversight.
Private trackers operate on an invite-only basis and usually require users to register. These communities are moderated.
Content is checked for quality and safety, and users who upload bad files are banned. While harder to access, private trackers offer a much safer environment.
Regardless of the source, you should always check the comments section and verify the reputation of the uploader before downloading any file.
System Protection
Even with a VPN and a trusted source, you should treat every downloaded file with caution. Real-time antivirus protection is essential.
You should scan every file immediately after the download completes and before you open or install it.
Configuring the torrent client itself is also an important safety step. Most clients allow you to force encryption on all connections, which adds another layer of security.
You should also set upload limits within the client settings. Unchecked uploading can saturate your connection, making standard web browsing impossible for anyone else on the network.
Conclusion
Torrenting remains one of the most efficient methods for sharing massive files across the internet. It transforms every user into a distributor to maximize speed and resilience in a way that traditional servers cannot match.
However, this power comes with significant responsibility regarding copyright laws and network security. You must use tools like VPNs and strictly verify your sources to protect your digital identity.
If approached with caution and the right software, the BitTorrent protocol is an invaluable resource for data distribution.
Frequently Asked Questions
Is torrenting illegal?
The act of torrenting itself is a legal file-sharing technology used for legitimate purposes like distributing open-source software. However, using it to download copyrighted material like movies or games without permission is illegal. The distinction lies entirely in the content you choose to download rather than the tool itself.
Do I need a VPN to torrent?
Using a VPN is highly recommended because it hides your IP address from other users in the swarm. Without one, your location and identity are visible to copyright trolls and hackers. A VPN also prevents your internet service provider from throttling your connection speed during transfers.
What is a seeder?
A seeder is a user who has downloaded the complete file and keeps their torrent client open to upload it to others. They are essential for the health of the swarm. If there are no seeders available, you cannot complete your download because the file data is missing.
Why is my torrent download so slow?
Slow speeds usually occur because there are not enough seeders to support the number of people trying to download the file. It can also happen if your specific network ports are blocked or if your internet provider is throttling P2P traffic. Checking your client settings often helps.
Can I get a virus from torrenting?
Yes, downloading files from public torrent sites carries a high risk of malware infection. Hackers often hide viruses inside files that appear to be popular movies or software. You should always scan downloaded files with antivirus software and read user comments before opening anything.


