What Is IPv6? Fixing the Address Shortage

Behind every website you load and message you send lies an invisible foundation directing data across the globe. Your devices need exact numerical coordinates to find and communicate with one another effectively.
For decades, the internet relied on a strictly limited pool of these addresses to function. The sudden explosion of smartphones, smart appliances, and connected cars quickly drained that original system.
We simply ran out of space.
To fix this severe shortage, engineers developed Internet Protocol version 6, commonly known as IPv6. This massive system upgrade provides the necessary infrastructure to keep global networking flowing without interruption.
It rescues the internet from gridlock by replacing the exhausted numbering format with a virtually infinite supply of fresh addresses. Without this vital protocol, our ability to connect new hardware to the web would completely stall.
The Anatomy of an IPv6 Address
To appreciate how the modern internet functions, one must look at the structure of its underlying addresses. The transition to a new protocol required a complete redesign of how devices are identified online.
The resulting format looks radically different from the familiar sequences of numbers most internet users are accustomed to seeing. This updated architecture brings massive mathematical scale and a new set of rules for displaying network coordinates.
128-Bit Architecture
The most significant change introduced by the new protocol is its sheer size. While older internet addresses relied on a 32-bit mathematical framework, the updated system utilizes a massive 128-bit structure.
This expansion creates an almost incomprehensible number of unique combinations. Specifically, the protocol provides over 340 undecillion distinct addresses.
To put that massive figure into perspective, there are enough unique combinations to assign an address to every single atom on the surface of the earth. This virtually infinite supply ensures humanity will never run out of network identifiers again, regardless of how many smart appliances or mobile phones enter the market.
Hexadecimal Formatting
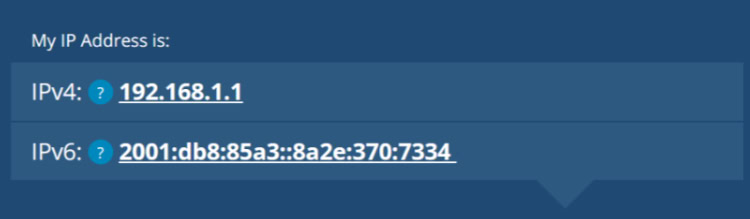
Because the new addresses are mathematically four times larger than their predecessors, displaying them using traditional numbers became impractical. Engineers shifted to a hexadecimal format to represent these massive strings of data.
Instead of just using the numbers 0 through 9, this alphanumeric system incorporates the letters A through F. Furthermore, the protocol abandons the familiar periods used to separate blocks of numbers.
An IPv6 address consists of eight distinct segments of four characters, and each segment is neatly divided by a colon.
Address Compression
A fully written 128-bit hexadecimal address is remarkably long and difficult to read. To make these identifiers practical for network administrators and everyday display, the protocol includes specific zero-omission rules.
If a segment within the address contains leading zeros, those zeros can be dropped. Additionally, if an address contains consecutive segments made entirely of zeros, they can be replaced entirely with a double colon.
These compression techniques condense an unwieldy string of characters into a significantly shorter format without changing the actual destination it points to.
Subnetting Structure
Despite the long string of characters, an IPv6 address is highly organized. The address is generally split down the middle into two distinct halves.
The first half acts as the routing prefix, which tells global routers exactly which network the data needs to reach. The Internet Service Provider typically assigns this portion.
The second half serves as the interface identifier. This specific identifier points directly to the exact device on that local network, whether it is a laptop, a smart television, or a gaming console.
This clear division makes directing traffic highly efficient.
IPv4 vs. IPv6: The Technical Shift
Transitioning between the two major internet protocols involves much more than just extending the length of an address. The jump from the fourth version to the sixth represents a fundamental change in how global network traffic is managed and delivered.
Engineers took the opportunity to fix long-standing inefficiencies, streamline data processing, and remove temporary fixes that had kept the older system running past its prime.
Capacity Breakdown
The primary motivation behind the transition was basic mathematics. The original 32-bit system offered roughly 4.3 billion unique combinations.
While that number seemed massive in the 1980s, the modern proliferation of internet-connected hardware exhausted that supply entirely. The updated 128-bit pool solves this mathematical constraint permanently.
By expanding the available supply to undecillions of addresses, the internet can continue to expand globally without the strict limitations that bottlenecked the older framework.
Header Simplification
Every piece of data sent across the internet is wrapped in a digital envelope called a packet header. This header contains the instructions routers need to deliver the information correctly.
The older protocol utilized a complex header loaded with optional fields that forced routers to perform extra processing work. The updated system streamlines this process significantly.
By moving non-essential information into extension headers and simplifying the main delivery instructions, routers can process and forward data packets much faster than before.
The End of NAT (Network Address Translation)
Under the older system, a severe shortage of addresses forced engineers to rely on Network Address Translation. This workaround allowed an entire household of devices to share a single public IP address while hiding behind a router.
Because the new protocol offers an infinite supply of unique combinations, this translation process is no longer required. Every individual phone, computer, and smart thermostat now receives its own dedicated, globally unique address.
This restores true end-to-end connectivity across the internet, allowing hardware to communicate directly without a router acting as an artificial middleman.
Data Delivery Methods
The older protocol relied heavily on a method called broadcasting. When a device needed to find a specific target, it would often shout its request to every single machine on the local network, creating unnecessary congestion.
The modern protocol abandons this noisy approach in favor of multicasting. Multicast messaging allows a device to send data only to the specific group of machines that actually need to hear it.
This precise delivery method significantly reduces wasted bandwidth and lightens the processing load on other hardware connected to the same network.
Built-In Advantages and Technical Benefits

Beyond expanding the raw supply of available addresses, the modern internet protocol introduces a suite of sophisticated technical improvements. The architects of the system designed it to handle the complex realities of modern networking, where users expect fast, secure, and highly mobile connections.
These baked-in advantages allow networks to operate with greater autonomy and precision.
Stateless Address Autoconfiguration (SLAAC)
Setting up a network connection historically required a centralized server to hand out addresses to new devices. The upgraded protocol introduces a feature that allows devices to configure their own network settings automatically.
When a new computer or smartphone connects to a network, it simply listens for a signal from the local router. Once it receives the network prefix, the device mathematically generates its own unique interface identifier.
This self-configuration process eliminates the need for dedicated address-assignment servers and makes network management remarkably straightforward.
Native IPsec Integration
Security was initially an afterthought in early internet design, requiring engineers to patch encryption protocols on top of existing connections later. The new standard changes this dynamic by natively integrating a security framework known as IPsec directly into the network layer.
This mandatory framework provides robust tools for encrypting data packets and authenticating the identity of the sender. While this security suite can also be applied to older networks, building it directly into the modern protocol ensures a baseline level of protection and privacy for data traveling across the web.
Seamless Device Mobility
Mobile phones frequently switch between cellular data towers and local wireless networks as users travel. Under older systems, changing access points meant receiving a brand new IP address, which immediately severed any active downloads or video calls.
The modern protocol includes built-in mobility features that allow a device to maintain its primary connection even as it physically moves between different networks. It utilizes a home address to anchor the connection and temporarily assigns a care-of address while roaming, ensuring that active data streams remain completely uninterrupted.
Optimized Global Routing
The explosive growth of the early internet resulted in a highly fragmented and inefficient routing table. Routers had to sift through massive lists of individual networks to figure out where to send traffic.
The modern protocol introduces a highly structured, hierarchical approach to address allocation. Internet Service Providers aggregate massive blocks of addresses logically, which significantly shrinks the global routing tables.
This organized hierarchy creates cleaner, more direct paths for internet traffic, allowing massive backbone routers to forward data with unparalleled efficiency.
Transition Hurdles and Implementation Challenges

Upgrading the fundamental language of the internet requires an enormous amount of global coordination. Replacing a deeply entrenched infrastructure is not as simple as flipping a switch to activate the new standard.
Engineers and network administrators face significant logistical hurdles as they integrate the updated framework into existing systems. This transition process demands careful planning to prevent widespread connectivity failures.
The Backward Compatibility Problem
The most pressing obstacle in rolling out the modern system is its inability to communicate natively with the older standard. The two protocols operate like completely distinct languages.
A computer running exclusively on the older format cannot directly exchange data with a server operating solely on the new one. This strict incompatibility forces the entire internet community to maintain two parallel networks at the exact same time.
Without a native bridge between the two formats, devices risk becoming isolated from large portions of the web.
Coexistence Strategies
To prevent network fragmentation, engineers rely on a series of specialized workarounds. The most common method is a dual-stack configuration, which allows routers and servers to process both versions of the protocol simultaneously.
When a dual-stack setup is not possible, networks utilize tunneling. This technique wraps the newer data packets inside older packet structures, allowing them to travel safely across legacy networks.
Additionally, specialized translation servers act as real-time interpreters. These servers intercept traffic from one protocol and translate it into the other, ensuring seamless communication across incompatible boundaries.
Readability and Management
The shift to a massive 128-bit architecture introduces severe usability challenges for human administrators. Network professionals spent decades memorizing simple 32-bit addresses to configure servers and troubleshoot connection errors.
The new alphanumeric sequences are far too long and complicated for reliable human memory. Manually typing these hexadecimal strings invites frequent typographical errors. Consequently, network management now relies heavily on automated tools and robust domain name systems.
Administrators must trust software interfaces to allocate, track, and monitor addresses instead of relying on manual data entry.
New Security Paradigms
The elimination of Network Address Translation drastically alters how personal hardware is secured. In older setups, home routers acted as a barrier, hiding local devices behind a single public connection.
Because the updated protocol assigns a unique, globally routable address to every single piece of hardware, that artificial shield disappears. Smart televisions, security cameras, and mobile phones are now directly exposed to the broader internet.
This exposure makes robust hardware firewalls an absolute necessity. Administrators and home users must enforce strict access policies to block malicious traffic from scanning and compromising their directly connected devices.
Practical Implications for Everyday Users

While network architects handle the complex technical challenges of the transition, regular internet users also experience the direct effects of this major upgrade. The new protocol touches many aspects of daily online life, influencing how home networks operate and how internet service providers deliver their connections.
Most of these changes occur quietly in the background. However, they actively shape performance metrics and influence online privacy standards for millions of individuals.
Impact on Internet Speed and Latency
Internet users frequently wonder if switching to the updated standard will make their browsing or online gaming noticeably faster. The protocol itself does not magically increase overall bandwidth.
However, it does eliminate the heavy processing overhead caused by Network Address Translation. Without the router pausing to rewrite packet headers for every single piece of data, connections often experience a slight reduction in latency.
Data travels along a more direct route from the server to the end user. Gamers and individuals using real-time communication software often benefit the most from this streamlined routing process.
Home Router Settings
Accessing the dashboard of a modern home router reveals specific configuration toggles for the new protocol. Many manufacturers ship their hardware with these settings enabled by default.
Leaving the functionality turned on allows the router to request and distribute modern addresses as soon as the internet service provider makes them available. Manually disabling this feature forces the home network to rely entirely on the older standard.
While turning it off might seem like a quick fix for isolated network glitches, doing so can restrict access to optimized routing paths and create software compatibility issues down the line.
Device and ISP Readiness
Determining if a household is actively using the modern standard requires looking at both personal hardware and the regional internet service provider. Almost all modern operating systems, including Windows, macOS, iOS, and Android, are fully equipped to handle the upgraded protocol right out of the box.
However, the final connection entirely depends on the service provider. If the regional telecom company has not updated its local infrastructure, the user remains tethered to the old system.
Individuals can quickly verify their status by visiting specialized testing websites that instantly analyze their active network connection.
Privacy Considerations
Assigning a permanent, globally unique address to a single smartphone or laptop creates valid privacy concerns. If a device retains the exact same address for years, advertisers and websites can easily track the user across the internet to build a detailed behavioral profile.
To combat this issue, modern operating systems implement privacy extensions. These extensions periodically generate randomized, temporary public addresses for all outward communication.
While the device maintains a static connection for its own local network, the face it shows to the public web changes constantly. This clever randomization process prevents third parties from using network coordinates as a reliable tracking tool.
Conclusion
Internet Protocol version 6 stands as the necessary, modern backbone of global networking. By replacing an exhausted numbering system, it ensures that the internet can continue expanding without artificial limits or convoluted workarounds.
This updated protocol successfully balances immense mathematical complexity with the highly practical need to connect billions of modern smart devices seamlessly. While the transition requires significant technical coordination globally, the resulting infrastructure guarantees that our communication networks remain fast, secure, and ready for future growth.
Frequently Asked Questions
Why did the internet need to upgrade to IPv6?
The original internet routing system completely ran out of available addresses due to the massive surge in personal computers and smartphones. Engineers created the newer protocol to provide a virtually infinite supply of unique identifiers. This upgrade ensures new hardware can always connect online without interruptions.
Will IPv6 make my internet connection faster?
Switching to the newer protocol does not directly increase your overall download speeds or bandwidth limits. However, it completely eliminates the need for network address translation. This streamlined routing process often results in lower latency, which improves responsiveness during online gaming and real-time video calls.
Should I enable IPv6 on my home router?
You should generally leave the modern protocol enabled on your home router if the manufacturer turns it on by default. Disabling this feature restricts your network to older routing methods. Keeping it active ensures your personal devices can utilize the most efficient paths available from your provider.
How is an IPv6 address different from IPv4?
The older format uses a simple 32-bit mathematical structure divided into four short blocks of standard numbers. The newer standard utilizes a massive 128-bit architecture written in hexadecimal format. This modernized alphanumeric structure includes letters and numbers separated by colons to accommodate the tremendous size increase.
Does using IPv6 negatively impact my online privacy?
Assigning a permanent public address to your smartphone or laptop could theoretically allow advertisers to track your activity. Modern operating systems prevent this entirely by using built-in privacy extensions. These tools routinely randomize your outward-facing network coordinates to block third parties from building accurate behavioral profiles.


