How to Create a Strong Password: Stop Hackers Today

Protecting your sensitive financial and personal data often relies entirely on a single line of text. Yet, as our online presence grows, password fatigue sets in rapidly.
We constantly struggle to balance the need for strict account security with the desire for everyday convenience. Memorizing dozens of unique logins feels impossible, causing many to reuse weak credentials and risk devastating breaches.
Fortunately, building an impenetrable defense does not require a superhuman memory. You will learn exactly what makes a passcode strong and the common pitfalls that leave accounts vulnerable.
The Anatomy of a Secure Password
Building a reliable defense starts with recognizing what makes a password truly robust against modern threats. Many people assume a complex jumble of characters is enough to keep intruders out.
However, true security involves specific mathematical realities that make guessing computationally impossible for malicious software.
Prioritizing Length Over Complexity
The number of characters in your password is the single most critical element in defeating automated cracking programs. Security experts universally recommend aiming for 12 to 16 characters at an absolute minimum.
Every single character you add exponentially increases the number of possible combinations a hacker's software must guess. A short password packed with rare symbols can often be cracked faster than a much longer phrase made entirely of lowercase letters.
Focusing on length provides a massive mathematical advantage, turning a task that might take a computer seconds into one that would take centuries.
Utilizing Character Variety
While length provides the foundation, mixing different types of characters acts as a massive multiplier for your security. Combining uppercase letters, lowercase letters, numbers, and special symbols forces cracking algorithms to draw from a much larger pool of possibilities.
If a password only uses lowercase letters, the computer only has 26 options per character spot. Adding uppercase letters doubles that number.
Throwing numbers and symbols into the mix creates an enormous matrix of potential combinations, severely hindering any attempt to systematically guess the correct sequence.
How Entropy Defeats Hackers
Entropy is a measure of unpredictability and randomness. In cybersecurity, high entropy means your password lacks any recognizable structure, making it a computer’s worst enemy.
Automated cracking programs are designed to look for logical patterns, common prefixes, and familiar linguistic rules. When a string of text possesses high entropy, it strips the software of its ability to make educated guesses.
The machine is forced to blindly try every possible combination. A truly random sequence maximizes entropy, neutralizing the sophisticated algorithms hackers rely on to break into accounts quickly.
Common Mistakes and Hacker Exploits

Even the most well-intentioned users frequently fall into predictable habits that compromise their accounts. Hackers rely heavily on these human flaws.
They exploit laziness and predictability to bypass security measures with frightening speed, often using specialized tools designed to capitalize on the exact shortcuts people take when creating their logins.
Relying on Personal Information
Using birthdates, pet names, street addresses, or family members' names leaves accounts highly vulnerable to targeted attacks. Hackers often gather this exact information from public social media profiles or background search websites.
Once an attacker compiles a profile on you, they will feed these personal details into their cracking software to generate custom guessing lists. A password based on your dog's name and your birth year is effectively public knowledge to an attacker willing to spend five minutes scrolling through your online presence.
Using Predictable Patterns
Keyboard walks like “qwerty” and sequential numbers like “123456” are completely useless against modern threats. These sequences are programmed into every basic cracking tool available.
Furthermore, people frequently rely on the exact same structural formula: capitalizing the first letter and putting a single exclamation mark at the very end. Hackers are well aware that “Password123!” is a popular format.
Their software automatically runs variations of this specific pattern, instantly bypassing passwords that users mistakenly believe are complex.
The Danger of Password Reuse
Using the exact same strong password across multiple websites creates a massive vulnerability known as credential stuffing. If a small, poorly secured forum you use suffers a data breach, hackers will acquire your email and password combination.
They then use automated bots to plug those same credentials into banks, email providers, and retail websites. If you recycle your logins, one single breach at an unrelated company completely compromises your entire digital identity.
Automated Cracking Methods
Cybercriminals rarely sit at a keyboard manually guessing passwords. Instead, they deploy dictionary attacks and brute-force methods to run through millions of weak guesses per second.
Dictionary attacks use massive lists of common words, phrases, and leaked passwords to systematically try every known language combination. Brute-force attacks simply cycle through every possible character combination starting from “a” and moving up.
If your login relies on a single dictionary word or lacks sufficient length, these automated tools will break it almost instantly.
Proven Techniques for Memorable Passwords

Creating a highly secure login does not mean you have to memorize absolute gibberish. You can apply simple, structured techniques to generate long, complex strings that stick in your mind naturally.
These methods leverage human memory processes while maintaining the strict unpredictability required to thwart malicious software.
The Passphrase Strategy
Moving away from random, unpronounceable text, the passphrase strategy involves combining four or more random, unrelated words. A string like “purple dinosaur coffee planet” creates extreme length that is highly secure but incredibly easy to visualize and remember.
Because the words have no grammatical connection to one another, cracking software cannot predict the sequence. This technique bypasses the frustration of memorizing complex character strings while simultaneously satisfying the vital requirement for extreme length.
The Sentence Transformation Method
If you struggle with random words, you can take a memorable sentence or song lyric and transform it into a complex string. By taking the first letter of each word in a personal sentence, you create a sequence that looks like gibberish to everyone else.
For example, “I bought my first blue car in nineteen ninety-nine” becomes “Ibmfbc1999!”. This method allows you to build a highly complex string of characters that is permanently locked in your memory through an easy-to-recall association.
Strategic Number and Symbol Placement
Injecting special characters and numbers into passphrases naturally adds security, provided you avoid easily guessable substitutions. Replacing an “a” with an “@” or an “s” with a “$” provides virtually no protection, as hackers program their bots to check for these exact substitutions first.
Instead, place numbers and symbols between words or at random intervals. Typing “purple?dinosaur99coffee!planet” breaks up the text unpredictably, significantly increasing the mathematical complexity without forcing you to memorize awkward character placements.
Managing Your Passwords Effectively
Managing dozens of distinct, highly secure logins quickly becomes impossible if you rely solely on your memory. Rather than resorting to writing sensitive information on sticky notes or recycling the same phrase across multiple sites, you can leverage purpose-built software to handle the heavy lifting.
Modern tools streamline the entire process of securing your accounts. They offer a practical solution to the memory burden that often leads to compromised data.
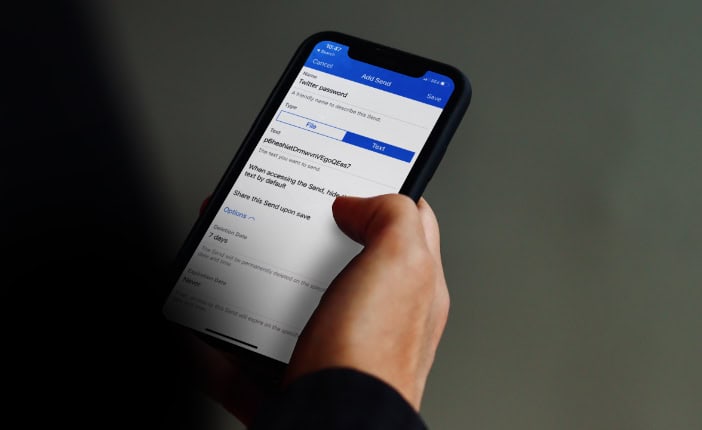
The Role of Password Managers
An encrypted digital vault serves as a centralized hub for all your credentials. These applications safely store your usernames and passphrases behind strict mathematical encryption algorithms.
By utilizing a password manager, you eliminate the need to memorize dozens of unique logins for your banking, email, and social media accounts. The software securely holds everything in one place and automatically fills in your details when you visit a recognized website.
This approach completely removes the temptation to reuse weak phrases, allowing you to maintain strict security protocols across every single platform you use.
The Master Password Concept
When you use a digital vault, your primary responsibility shifts from memorizing many credentials to protecting just one. This central login is known as your master password.
You can focus all your mental energy on creating one exceptionally strong, incredibly long passphrase. Because this single string of text unlocks your entire vault, it must be the most robust credential you possess.
By applying the passphrase strategy here, you construct an impenetrable barrier that only you can bypass. You trade the frustration of constant password resets for the simplicity of remembering a single, vivid sentence.
Utilizing Built-In Generators
Most modern vault applications include a built-in generator that automatically creates long, random strings of characters for all your new accounts. Instead of struggling to invent a secure combination, you simply allow the software to instantly generate a 20-character string of letters, numbers, and symbols.
The application then saves this sequence and autofills it during future visits. This process entirely removes human error and predictability from the equation. You never even need to look at the generated text, ensuring that the credentials remain entirely random and completely resistant to automated cracking techniques.
Layering Defenses Beyond the Password

Even the most complex and tightly guarded password can sometimes fall into the wrong hands through phishing scams or massive corporate data breaches. Because single-point failures happen frequently, relying exclusively on a password leaves your personal information exposed.
Adding secondary verification steps ensures that an attacker cannot access your accounts even if they successfully steal your login credentials. Layering your defenses creates a robust system that stops unauthorized access attempts immediately.
The Necessity of Multi-Factor Authentication
Multi-factor authentication requires you to provide a second piece of evidence to prove your identity before granting access to an account. A password alone should never stand as your only line of defense.
By enabling this secondary step, you create a physical barrier that remote hackers cannot bypass easily. If a cybercriminal steals your login details from a compromised website, they still cannot access your bank or email without physical possession of your mobile phone or security token.
This secondary requirement dramatically reduces the success rate of unauthorized login attempts and provides immediate alerts if someone tries to breach your account.
Evaluating Authentication Methods
Not all secondary verification methods offer the same level of protection against determined attackers. Many services default to sending SMS text messages containing a temporary code.
While better than nothing, SMS messages are vulnerable to SIM-swapping attacks, where a hacker tricks your cellular provider into transferring your phone number to their device. Dedicated authenticator applications offer a vastly superior alternative.
These apps generate local, time-based codes directly on your device without relying on vulnerable cellular networks. By using an authenticator app, you cut off remote interception vectors and ensure the temporary codes remain strictly in your physical possession.
Securing Backup Codes
When you set up secondary authentication, the service will provide a list of one-time recovery codes. These backup codes are essential lifelines designed to prevent permanent account lockouts if you ever lose your phone or accidentally delete your authenticator application.
Properly securing these recovery strings is an absolute necessity. You should print them out and store the physical copy in a secure location like a fireproof safe or a locked filing cabinet.
Treat these codes with the exact same level of caution as your social security card or passport, as anyone who finds them can bypass your carefully constructed security layers entirely.
Conclusion
Securing your personal information requires prioritizing character length and ensuring strict uniqueness across all your accounts. Attempting to remember dozens of complex strings inevitably leads to frustration and repeated mistakes.
Instead, you should utilize dedicated management software to relieve the memory burden and completely automate the generation process. Establishing a solid defense strategy provides long-term peace of mind.
By applying these practical methods, you significantly reduce the risk of identity theft and protect yourself from devastating security breaches.
Frequently Asked Questions
How often should I change my passwords?
You only need to change your password if you suspect an unauthorized login or if a company notifies you of a data breach. Frequently updating credentials often weakens overall security. People tend to make minor, predictable tweaks to their old phrases rather than creating entirely new ones.
Are password managers completely safe to use?
Password managers are highly secure and rely on advanced mathematical encryption to protect your data. Even if a provider suffers a breach, your vault remains unreadable without your master passphrase. Using one is significantly safer than relying on your memory or recycling weak logins.
Why is a long passphrase better than a short complex password?
Automated cracking programs can guess short sequences in fractions of a second, regardless of how many special symbols you include. A longer passphrase exponentially increases the mathematical difficulty of guessing the sequence. Length defeats automated software far more effectively than random, complicated symbols.
Can I write my passwords down on paper?
Writing your credentials in a physical notebook is much safer than storing them in an unprotected document on your computer. If you choose this method, you must store the paper in a highly secure physical location like a fireproof safe to prevent unauthorized physical access.
What should I do if my account is hacked?
If you suspect an unauthorized login, immediately reset the compromised credential and update any other accounts sharing that same phrase. Next, enable multi-factor authentication to block further unauthorized access. Finally, review your recent account activity and report any suspicious transactions to your financial institution.


