How to Prevent Malware: Secure Your Devices Now

It takes only one accidental click on a suspicious link to expose your bank login credentials or lock every family photo behind a million dollar ransom. Once malicious software like ransomware or trojans embed themselves into your devices, the damage to your finances and privacy can be permanent.
These threats act as silent intruders that track your typing or hijack your processing power. While many people believe they can simply fix an infection after the fact, scrubbing a system is far more expensive and stressful than stopping an intrusion before it starts.
Relying on a single antivirus program is no longer sufficient for modern security. Strengthening your defense requires a strategy that covers every point of entry, from your home router to your daily browsing habits.
Key Takeaways
- Implement the 3-2-1 backup strategy by keeping three copies of data on two different media types, with one version stored securely off-site.
- Enable multi-factor authentication on all sensitive accounts to provide a secondary defense layer if a password is ever compromised.
- Isolate smart home devices on a separate guest network to prevent them from becoming entry points to your primary computer or tablet.
- Use standard user accounts for daily tasks rather than administrator accounts to restrict how much of your system a virus can modify.
- Identify social engineering by checking sender addresses for errors and hovering over links to confirm they lead to official websites before clicking.
Technical Safeguards
Establishing a strong technical foundation is the first step toward securing any system. These automated tools work in the background to filter out threats before they reach your data.
By combining reactive scanning with proactive traffic control, you build a perimeter that catches the majority of automated attacks.
Advanced Anti-Malware Solutions
Modern security software has moved far beyond simple virus databases. Contemporary suites use behavioral analysis to monitor how programs act.
If a file begins encrypting documents or attempting to modify system files without permission, the software can block it even if the threat has never been seen before. AI driven detection further enhances this by recognizing patterns typical of malicious activity, providing a layer of protection against zero day exploits.
Active Firewall Management
Firewalls act as gatekeepers for your internet connection. A software firewall runs on your computer to manage which applications can talk to the internet, while a hardware firewall is often built into your router to protect every device in the house.
You should verify that these are active and configured to block unsolicited incoming connections. Monitoring outbound traffic is equally important, as it can alert you if a hidden program is trying to send your personal data to a remote server.
Automated Software Patching
Hackers frequently exploit known software bugs to gain unauthorized access. Software developers regularly release patches to fix these security holes.
You should enable automatic updates for your operating system, web browsers, and all third party applications. Delaying an update by even a few days can leave a window of opportunity for attackers who scan the internet for unpatched systems.
Keeping every piece of software current is one of the most effective ways to reduce your risk.
Digital Hygiene

Even the best security software cannot protect a system if a user inadvertently invites a threat inside. Digital hygiene refers to the habits and routines that keep your online presence clean and safe.
Maintaining a skeptical mindset while interacting with messages and websites prevents most common infections.
Recognizing Social Engineering
Social engineering involves tricking people into giving up information or installing malicious files. Phishing emails often use a sense of urgency, such as a fake bank alert or a package delivery notification, to make you click a link. Be wary of any message that asks for sensitive data or contains unexpected attachments.
Check the sender’s email address for slight misspellings and hover over links to see the actual destination before clicking. This caution should extend to text messages and instant messaging apps.
Safe Browsing Habits
The websites you visit can host malicious scripts that download software without your knowledge. You should prioritize sites that use encrypted connections, often signaled by a padlock icon in the address bar.
Avoid visiting high risk areas of the internet, such as pirated content sites or unverified forums. Security extensions for your browser can add an extra layer of safety by blocking malicious scripts and tracking cookies that could lead to suspicious domains.
Verified Download Sources
Malware is frequently hidden inside legitimate looking software. To avoid this, only download programs from official sources like the Microsoft Store, Apple App Store, or the developer’s verified website.
Third party download portals often bundle additional, unwanted software with the file you actually want. This extra software can include adware or spyware that slows down your computer and compromises your privacy.
Hardened Access and Identity
Securing how you log into your accounts is just as important as securing the devices themselves. If an attacker gains your credentials, they can bypass many technical safeguards.
Hardening your identity involves making passwords impossible to guess and adding verification steps that require your physical presence.
Credential Management
Reusing the same password across multiple sites is a major security risk. If one site suffers a data breach, every other account using that password becomes vulnerable.
Instead of trying to remember dozens of complex strings, use an encrypted password manager to generate and store unique, long passphrases for every service. These managers ensure that even if one account is compromised, the rest of your information remains safe behind a single, strong master password.
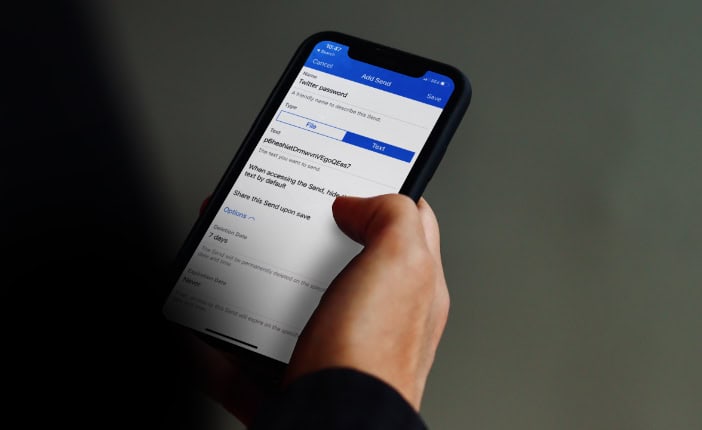
Multi-Factor Authentication
Multi-factor authentication adds a second step to the login process. Even if a criminal steals your password, they cannot access your account without a secondary code from an app on your phone or a physical security token.
Avoid using SMS based codes when possible, as these can be intercepted. Using an authenticator app or a hardware token provides much higher security against sophisticated remote attacks.
The Principle of Least Privilege
Many people use their computers while logged into an administrator account, which has the power to change any system setting. If malware infects an admin account, it gains that same power.
By using a standard user account for daily tasks like web browsing and document editing, you limit the damage a virus can do. The system will prompt for an admin password before any major changes occur, giving you a chance to stop an unauthorized installation.
Secure Network and Device Environments

The security of your computer is tied to the security of the network it uses. An unprotected home network or a risky public connection can expose your data to everyone nearby.
Properly configuring your hardware and isolating different types of devices creates a controlled environment that is much harder for attackers to penetrate.
Home Router Security
Your router is the front door to your home network. You should immediately change the default administrative username and password that came with the device, as these are well known to hackers.
Ensure your Wi-Fi is protected with WPA3 encryption, or at least WPA2. Additionally, disable features like Wi-Fi Protected Setup (WPS) and Universal Plug and Play (UPnP), which can create easy entry points for intruders.
Public Network Protection
Public Wi-Fi networks in cafes or airports are often unencrypted and monitored by malicious actors. When you must use these networks, a Virtual Private Network (VPN) encrypts your traffic, making it unreadable to others on the same connection.
If a VPN is unavailable, using a cellular hotspot from your phone is a much safer alternative than connecting to an open public access point.
IoT and Secondary Device Isolation
Smart home devices, such as cameras and thermostats, often have weaker security than computers. If one of these devices is compromised, it can be used to attack other machines on the same network.
Most modern routers allow you to create a guest network. By placing all smart home gadgets and older devices on this isolated network, you ensure that a breach in a lightbulb does not lead to a breach of your primary computer.
Resilience and Monitoring

Security is not just about stopping an attack, but also about how quickly you can recover if one succeeds. Building resilience means having a plan for data recovery and knowing how to spot the signs of a problem before it escalates.
Regular monitoring helps you catch infections in their early stages.
The 3-2-1 Backup Strategy
A reliable backup is the only guaranteed way to recover from a ransomware attack. Follow the 3-2-1 rule: keep three copies of your data, store them on two different types of media, and keep one copy off-site.
For example, you might have your original files on your PC, a backup on an external hard drive, and a second backup in an encrypted cloud service. Ensuring that at least one backup is disconnected from the network prevents malware from infecting your recovery files.
Identifying Red Flags
Knowing when something is wrong allows you to act before your data is lost. Look for signs like a sudden drop in system performance, programs opening and closing on their own, or your fan running at high speeds when you aren’t doing anything intensive.
Unusual network activity or notifications about unauthorized password resets are also major warning signs. If your computer starts behaving strangely, it is better to assume an infection and begin an investigation.
Pre-Infection Response Readiness
If you suspect a device is infected, you must act quickly to contain the threat. Disconnect the machine from the internet immediately by turning off Wi-Fi or unplugging the ethernet cable.
This stops the malware from communicating with its creator or spreading to other devices on your network. Having a bootable rescue drive prepared in advance can help you scan and clean the system without starting the infected operating system.
Conclusion
Effective digital security does not require a massive budget or deep technical expertise. Instead, staying safe relies on the consistent application of simple habits like updating software and using a password manager.
Because new threats emerge every day, maintaining your defenses is a continuous commitment to staying informed and proactive. While no system is perfectly impenetrable, these layered strategies significantly reduce your risk.
Taking these steps provides the confidence to use the internet safely, knowing your personal information and financial records are well protected from external interference.
Frequently Asked Questions
Is free antivirus software actually enough to keep me safe?
Free antivirus provides basic protection, but it often lacks the advanced behavioral analysis and firewall management found in paid suites. Modern threats frequently bypass simple scanners by changing their code constantly. A comprehensive security suite offers multiple layers of defense that better handle sophisticated attacks like ransomware and zero day exploits.
Do I really need a VPN when I am just using the Wi-Fi at a local coffee shop?
You should always use a VPN on public Wi-Fi to encrypt your data and prevent others on the same network from seeing your activity. Unsecured public connections are easy targets for hackers who want to intercept login credentials or personal information. A VPN creates a secure tunnel that keeps your browsing private.
Why should I bother with a password manager if I have a good memory?
A password manager is necessary because it allows you to use unique, complex passphrases for every account without having to memorize them. Reusing even a strong password is dangerous if one of the sites you use suffers a data breach. Managers also help protect against phishing by only filling credentials on legitimate sites.
What should I do first if I think my computer has a virus?
You must immediately disconnect your device from the internet to stop the infection from spreading or communicating with an external server. Once isolated, you should run a full system scan using a trusted security suite or a bootable rescue drive. Changing your account passwords from a separate, clean device is also vital.
Does keeping my computer updated really stop hackers?
Regular updates are essential because they patch security vulnerabilities that hackers use to gain remote access to your system. Most automated attacks target known bugs in operating systems or browsers that have already been fixed by developers. By enabling automatic updates, you close these doors before an attacker can walk through them.


