Pros and Cons of a Password Manager: Boost Your Safety

The average person maintains dozens of online accounts, but most rely on a handful of predictable, recycled phrases to secure them. This habit creates a massive vulnerability, as one leaked credential can grant access to an entire identity.
Password managers attempt to solve this crisis by acting as a highly encrypted vault. They generate and store unique, random strings for every site; the user only needs to remember a single master password.
While these tools offer a significant boost to safety and convenience, they also introduce a centralized point of failure. Handing every secret to a single piece of software requires a clear look at the trade-offs involved.
Key Takeaways
- Password managers remove the danger of password reuse by creating unique, complex strings for every account you own.
- Zero-knowledge architecture ensures that only you can see your data, as the service provider cannot access your encrypted vault.
- The master phrase is a sensitive point of failure that requires a strong password and secondary authentication for protection.
- Browser tools provide basic ease of use, while standalone applications offer more robust features and independent security audits.
- Initial setup takes time to organize and update old accounts, but it results in a massive improvement to your safety profile.
Security Advantages and Advanced Protection
Password managers provide a layer of defense that manual habits cannot match. By automating complex tasks and using high level encryption, these tools move beyond simple storage to actively protect data from common attacks.
They replace human error with mathematical precision; making it much harder for criminals to gain access through simple guesswork or large scale leaks.
Automatic Password Generation
Human memory is ill-suited for creating truly random data. Most people fall into predictable patterns, such as using names, dates, or repetitive symbols that automated cracking tools can guess in seconds.
A password manager removes this burden by generating long strings of randomized characters. These passwords include a mix of uppercase letters, numbers, and symbols that lack any personal meaning or linguistic structure.
Since the software remembers these strings for you, there is no longer a need to sacrifice complexity for memorability.
Zero-Knowledge Architecture
Standard security protocols for these services rely on a zero-knowledge framework. This means the service provider encrypts your data using your master password before it ever leaves your device.
The company never sees your actual passwords or the master phrase used to unlock them. Even if the provider’s servers are hacked or their employees are pressured to hand over information, the data remains scrambled and unreadable.
The only person with the code to unlock the vault is the individual user.
Guarding Against Phishing
Phishing attacks often involve fake websites that look identical to a bank or social media login page. While a human might be fooled by a slightly altered URL, a password manager is not.
These tools link credentials to specific, verified web addresses. If you land on a suspicious or unrecognized site, the software will refuse to autofill your information.
This immediate red flag serves as a critical warning that you are on a fraudulent page, preventing you from accidentally handing over your credentials to a scammer.
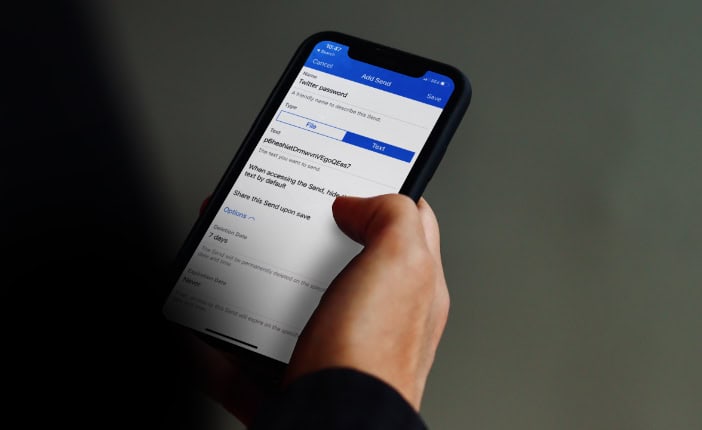
Encrypted Data Sharing
Sharing logins for utilities, streaming services, or business accounts often leads to security lapses. Many people send these details via text message or email, where they remain in plain text and vulnerable to interception.
Professional vault services include secure sharing folders that encrypt the data during transit and storage. This allows multiple people to access a shared account without ever exposing the actual password in an unsecure format.
Efficiency and User Experience

Safety does not have to come at the cost of speed. These applications focus on streamlining daily tasks by reducing the friction of logging into accounts and managing personal information.
By centralizing sensitive data into a single interface, they make the internet easier to use while maintaining high standards for every account you own.
Access Across Multiple Devices
Modern life requires switching between phones, laptops, and tablets throughout the day. A cloud based password manager ensures that when you update a password on your desktop, it is immediately available on your mobile device.
This synchronization eliminates the frustration of being locked out of an account because you changed a credential on a different machine. It provides a consistent experience regardless of which operating system or browser you prefer to use.
Intelligent Autofill and Form Completion
Beyond managing login credentials, these tools act as personal assistants for data entry. They can securely store credit card numbers, shipping addresses, and contact details.
When you reach a checkout page or a registration form, the software populates every field with a single click. Some advanced versions even handle multi-factor authentication by generating and filling in one time security codes, removing the need to check your phone for a text message every time you log in.
Dark Web and Breach Alerts
Many password managers include passive monitoring services that scan the corners of the internet for your information. If a website you use suffers a data breach, the password manager will alert you immediately.
It identifies which of your stored accounts are compromised and prompts you to change those passwords before they can be used by bad actors. This proactive approach ensures that you stay ahead of threats rather than reacting only after your accounts have been accessed.
Digital Legacy and Emergency Rights
Planning for the future includes managing your digital assets. Many vault services offer features that allow you to designate a trusted person to receive access in specific circumstances.
If you are incapacitated or pass away, these individuals can request access to your vault. There is typically a waiting period where you can deny the request, but if no action is taken, the software grants them entry.
This ensures that your family can manage your affairs and preserve your digital legacy without a legal battle.
Risks and Technical Vulnerabilities
No security tool is perfect; relying on a single service for all security needs carries inherent dangers. Identifying these weak points allows you to take extra precautions and maintain a realistic view of your safety.
While these tools solve many problems, they also create a new set of challenges that require careful management.
The Concentrated Risk of a Single Vault
The most significant drawback is the creation of a single point of failure. When you store every credential in one place, the security of your entire online identity rests on the strength of your master password.
If an attacker manages to obtain that one phrase, they gain total access to your banking, email, and personal accounts. This concentration of risk makes it vital to use a unique, extremely strong master phrase and to protect it with every available secondary security layer.
High Value Targets for Cyberattacks
Because password managers store the secrets of millions of people, the companies that run them are massive targets for hackers. These “honeypots” attract the most sophisticated cybercriminals in the world.
While these companies have professional security teams and robust infrastructure, they are under constant attack. Users must trust that the company’s internal defenses are strong enough to withstand these persistent threats and that their encryption methods remain current.
Dependency and Data Loss
A high level of security can sometimes lead to a permanent lockout. Because of the zero-knowledge design, most companies cannot reset your master password or recover your data if you forget your credentials.
If you lose your master phrase and your physical recovery codes, your data is gone forever. This total dependency on a single piece of information can be a liability for users who are prone to forgetting passwords or who do not keep physical backups of their recovery information.
Local Threats and Malware
Even the best encryption cannot protect you if your physical device is compromised. If a computer is infected with malware like a keylogger, it can record every stroke you type, including your master password.
Once an attacker has that phrase, the encryption on the vault becomes irrelevant. This means the security of your password manager is ultimately tied to the health of your hardware.
Using a vault on an unsecure public computer or a virus ridden laptop creates a massive hole in an otherwise strong defense.
Implementation Options and Comparisons

Choosing the right tool depends on your technical comfort and how much you are willing to pay for convenience. There are three main categories of software, each offering a different balance of accessibility and control.
Selecting the right version requires evaluating how you use your devices and how much trust you are willing to place in cloud-based services.
Browser-Integrated Solutions
Most popular web browsers like Chrome, Safari, and Firefox offer built-in password management for free. These tools are incredibly convenient because they require no extra installation and prompt you to save credentials as you browse.
For casual users who primarily use one type of device, this is often the easiest entry point. However, these password managers frequently lack robust cross-platform functionality.
Using your saved passwords from a desktop browser on a different mobile operating system can be difficult. Additionally, they often lack the deep security isolation found in dedicated apps, making them slightly more vulnerable if someone gains access to your logged-in browser profile.
Independent Dedicated Applications
Third-party applications such as Bitwarden and 1Password are designed specifically for high-level security. These services usually provide superior encryption methods and undergo frequent independent security audits to prove their reliability.
They offer advanced features that browsers do not, including alerts for data breaches and secure storage for sensitive documents. Users must also manage a separate piece of software, which adds an extra step to their digital routine.
Local and Offline Vaults
For those who are uncomfortable storing sensitive data on a company’s server, local vaults like KeePass provide an alternative. These tools store your encrypted database file directly on your computer or a private USB drive.
This eliminates the risk of a cloud-service provider being hacked; the data never touches the internet unless you move it yourself. The downside is a significant loss of convenience.
Users must manually sync their database across devices, and these programs often lack the seamless autofill capabilities that make cloud-based password managers so efficient.
User Trade-offs and Practical Realities

Adopting a management tool requires more than just a software download. It involves a change in daily habits and a period of adjustment while you organize your data.
Understanding the practical limitations and the effort required for setup will help you maintain realistic expectations about how these tools function in daily life.
Setup and Migration Demands
The initial transition is the most time-consuming part of the process. You must import your existing credentials and, more importantly, audit them.
Most users find that once they start the process, they have dozens of old, weak, or reused passwords that need to be updated. Replacing these with unique, randomized strings can take several hours or even days depending on the number of accounts you own.
While this one-time investment significantly improves your safety, the learning curve and initial effort can be a barrier for those seeking an instant fix.
Free versus Subscription Costs
While many basic versions of these tools are available for free, the most powerful features are often locked behind a paywall. Paid plans usually include family sharing options, larger encrypted file storage, and advanced multi-factor authentication support.
You must evaluate whether these additions justify a recurring cost. For many families or professionals, the ability to securely share logins is worth the price, but individual users may find that a free version of a reputable service meets all their basic requirements.
Website and App Compatibility
Even the most advanced software can run into technical hurdles. Some highly secure websites, particularly those for banking or government services, use code that intentionally blocks autofill functionality to prevent automated attacks.
In these cases, the password manager may fail to recognize the fields, forcing you to manually copy and paste your username and password. While this is a minor annoyance, it can disrupt the smooth experience that users expect from a modern management tool.
The Role of Personal Discipline
A password manager is a powerful tool, but its effectiveness is entirely dependent on the user. It is only as secure as the master password used to lock the vault.
If you choose a weak master phrase or fail to enable multi-factor authentication, you leave the door open for attackers. Using these tools correctly requires the discipline to never reuse the master password elsewhere and to keep your recovery codes in a safe, physical location.
The software provides the infrastructure for safety, but the user must provide the commitment to follow best practices.
Conclusion
Expert consensus favors these tools because they solve the most common security failure: human memory. While a centralized vault has risks, they are manageable compared to the dangers of password recycling.
The best choice depends on your budget and technical comfort. Shifting your focus toward these tools is about achieving a massive reduction in risk rather than finding an impossible, perfect solution.
Frequently Asked Questions
Is it safe to store all my credentials in one place?
Storing everything in a single vault creates a central target, but it is much safer than using weak or repeated passwords. These tools use high level encryption that makes it almost impossible for hackers to read your data without your master phrase. Adding multi-factor authentication provides a necessary secondary layer of defense.
What happens if I forget my master password?
Most modern password managers use zero-knowledge encryption, meaning they cannot reset your password for you. If you lose your master phrase and your recovery code, you will permanently lose access to all stored data. It is vital to write down your recovery code and store it in a secure, physical location.
Are free password managers secure enough for daily use?
Reputable free versions often provide the same level of encryption as their paid counterparts. The difference usually lies in extra features like file storage or family sharing rather than the core security technology. As long as the provider has a strong reputation and uses zero-knowledge architecture, a free plan is a great choice.
Can a password manager work on both my phone and computer?
Most dedicated and browser based solutions offer seamless syncing across different devices and operating systems. When you save a new login on your laptop, the software automatically updates the entry on your smartphone. This ensures you always have access to your credentials regardless of which machine you are using at the moment.
Do I still need to use two-factor authentication?
Yes, a password manager should be your first line of defense, but two-factor authentication adds a critical secondary layer. Even if someone steals your master password, they would still need your secondary code to enter the vault. Using both together creates a much stronger barrier against unauthorized access to your online identity.


