Search Engine Keeps Changing to Yahoo? Here’s the Fix

You open your browser for a quick search, hit enter, and suddenly find yourself staring at a Yahoo results page. You change your default engine back to your preferred choice, but the very next day, the exact same thing happens.
This relentless “Yahoo redirect” is a notorious problem that frustrates millions of users.
Beyond delivering clunky and less accurate search results, this endless loop creates a serious sense of unease. A browser that ignores your direct commands usually signals a compromised machine, leaving you wondering what else might be operating behind the scenes.
Key Takeaways
- Browser hijackers are hidden scripts that modify your default settings to generate illicit advertising revenue.
- Restoring your browser requires deleting unauthorized search engines and manually resetting the application to its original defaults.
- Malicious extensions and hidden background apps are usually the culprits forcing the relentless redirect loop.
- Running a dedicated antimalware scan is absolutely necessary to identify and remove deeply embedded system threats.
- Selecting custom installation paths for new downloads prevents unwanted software from bundling onto your computer.
Understanding the Root Causes of Search Engine Hijacking
When your browser stubbornly refuses to use your selected search tools, you are dealing with a forced override. The software is no longer following your commands because an external program or script is actively intercepting your web traffic.
Figuring out how this unauthorized software gained access to your system is an important first step in permanently removing it.
Browser Hijackers and Malware
Malicious developers create browser hijackers specifically to generate illicit advertising revenue. By forcing your daily web queries through a specific portal like Yahoo, these threat actors collect money for the traffic they deliver to the search provider.
This malicious code embeds itself deeply into your browser registry, making it incredibly resilient against basic setting adjustments. Until the underlying code is found and removed, the hijacker will simply reapply the Yahoo redirect every time you launch the browser.
The Role of Software Bundling
Most users do not intentionally install browser hijackers. Instead, these frustrating tools arrive as Potentially Unwanted Programs (PUPs) hidden within legitimate free software downloads.
When you download a free media player or document converter, the installation wizard often includes pre-checked boxes granting permission to change your default search engine. If you quickly click through the setup screens without reading the fine print, the bundled software silently installs itself in the background.
Legitimate Software Interference
Not every search redirect is the result of malicious activity. Frequently, trusted software applications are the actual culprits.
Many popular antivirus programs and system optimization tools include proprietary “safe search” utilities designed to filter out dangerous websites. These security suites will deliberately alter your browser preferences to route your queries through their partnered search engines, which is often Yahoo.
If you have recently installed or updated your security software, its built-in web protection features might be overriding your manual choices.
Browser-Level Configuration and Restoration

To break the redirect loop, you must first clear out the corrupted configurations inside your browser application. This process involves manually pointing the software back to your preferred provider and wiping out the hidden databases where hijackers store their settings.
Because every browser has a unique interface, the exact steps to accomplish this will depend on the software you use.
Manually Resetting Default Search Engines
The first corrective action is overriding the forced Yahoo redirect by manually assigning a new primary search provider. You must explicitly tell the browser where to send your queries.
Google Chrome:
- Click the three vertical dots in the top right corner and select “Settings”.
- Click “Search engine” on the left sidebar.
- Locate the dropdown menu labeled “Search engine used in the address bar”.
- Click the menu and select your preferred option, such as Google, Bing, or DuckDuckGo.
- Open a new tab and run a test query to confirm the immediate change has taken effect.
Microsoft Edge:
- Click the three horizontal dots in the top right corner and select “Settings”.
- Click “Privacy, search, and services” on the left sidebar.
- Scroll all the way to the bottom of the page and click “Search and connected experiences”.
- Click on “Address bar and search”.
- Click the dropdown menu next to “Search engine used in the address bar” and choose your preferred provider.
- Open a new tab to test your configuration.
Apple Safari:
- Open the browser, click “Safari” in the top menu bar, and select “Settings”.
- Click the “Search” tab located at the top of the window.
- Click the dropdown menu next to “Search engine” and select your actual preference.
- Open a new tab and perform a search to verify the fix.
Cleaning the “Managed Search Engines” List
Hijackers often hide backup configurations inside your browser’s secondary search list. If you do not delete Yahoo from this specific internal database, the unwanted redirects will eventually return.
Google Chrome:
- Navigate back to the “Search engine” section in your settings.
- Click the option labeled “Manage search engines and site search”.
- Scroll down to the “Search engines” list. You will likely see Yahoo listed here, alongside unrecognizable entries like “Search Helper”.
- Click the three vertical dots next to any unauthorized search engine.
- Select “Delete” from the popup menu. Repeat this until only your preferred search engines remain.
Microsoft Edge:
- Navigate back to the “Address bar and search” section in your settings.
- Click the option labeled “Search engines”.
- Review the list of installed search providers for Yahoo or any suspicious entries.
- Click the three horizontal dots next to the unwanted engine and select “Remove”.
- Repeat the process to clear out all unauthorized items.
Apple Safari:
- Safari handles secondary searches differently, but hijackers often exploit the “Quick Website Search” feature or install hidden system profiles.
- In the Safari “Search” settings tab, click “Manage Websites” next to “Quick Website Search”.
- Highlight any unfamiliar websites listed and click “Remove”, then click “Done”.
- Next, open your Mac’s “System Settings”, search for “Profiles” in the search bar, and delete any unfamiliar configuration profiles that might be forcing a search engine change.
Resetting Browser Settings to Default
If manual adjustments fail, utilizing a complete reset is the most effective way to eliminate hidden configuration changes. This action wipes out unauthorized modifications while safely preserving your personal data like saved passwords and bookmarks.
Google Chrome:
- Open your browser settings and click “Reset settings” on the left sidebar.
- Click the option titled “Restore settings to their original defaults”.
- A warning box will appear explaining that this action will disable extensions, clear cookies, and reset your startup page.
- Click the “Reset settings” button to confirm.
- Restart your browser to launch the application with a clean slate.
Microsoft Edge:
- Open your browser settings and click “Reset settings” on the left sidebar.
- Click “Restore settings to their default values”.
- Read the warning prompt detailing the data that will be cleared.
- Click the “Reset” button to execute the wipe.
- Close and reopen Edge to finalize the changes.
Apple Safari:
- Safari no longer has a single reset button, so you must clear its data manually. Click “Safari” in the top menu bar and select “Clear History”.
- Select “All History” from the dropdown and click “Clear History”.
- Next, click “Safari” in the top menu bar and select “Settings”.
- Go to the “Advanced” tab and check the box at the very bottom labeled “Show features for web developers”.
- A new “Develop” option will appear in your top menu bar. Click “Develop” and select “Empty Caches”.
- Quit and reopen Safari.
Auditing and Removing Malicious Extensions
If you successfully clean your browser settings but the Yahoo redirect immediately returns, an extension is actively reverting your changes. Identifying and uninstalling these rogue add-ons across your specific browser platform is absolutely necessary to secure your system.
Identifying Suspicious Add-ons
Malicious extensions are designed to look harmless. You must carefully audit your installed tools to find the specific program causing the interference.
Google Chrome:
- Click the puzzle piece icon near your address bar and select “Manage extensions”.
- Scan the page for programs with vague, generic names like “PDF Converter” or “Search Enhancer”. Look for items you do not remember installing.
- Pay close attention to any extension displaying a “Managed by your organization” badge, as hijackers frequently use enterprise policies to lock themselves in.
- Click “Details” on suspicious extensions to review their permissions.
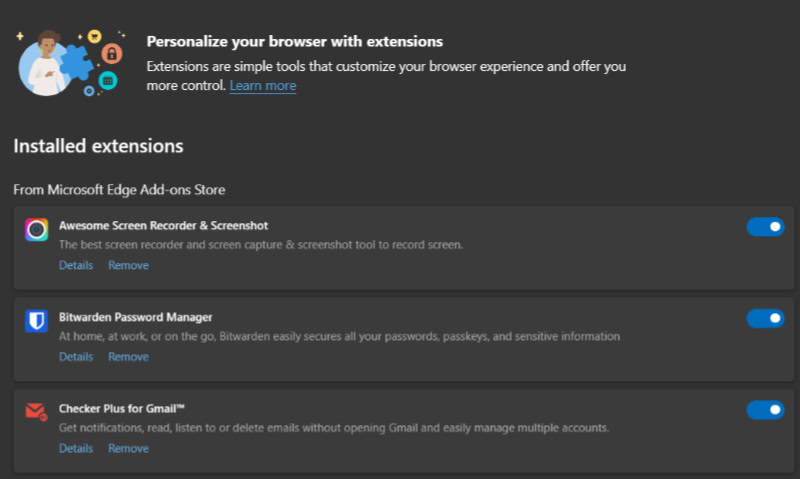
Microsoft Edge:
- Click the puzzle piece icon near your address bar and select “Manage extensions”.
- Review the list of active add-ons for anything unfamiliar or suspicious.
- Check for extensions claiming to be “Safe Search” tools or weather alerts, as these frequently harbor redirect scripts.
- Click “Details” to see what data the extension is allowed to read and modify.
Apple Safari:
- Open Safari, click “Safari” in the top menu bar, and select “Settings”.
- Click the “Extensions” tab located at the top of the window.
- Browse the list on the left side of the window for unrecognizable applications.
- Select an extension to view its description and permissions on the right side of the screen.
The Removal Process
Properly removing a malicious extension requires more than just hiding it from your toolbar. You must completely uninstall the program and ensure your browser’s synchronization features do not automatically redownload it.
Google Chrome:
- In the “Manage extensions” menu, locate the suspicious add-on.
- Click the “Remove” button directly beneath the extension’s name.
- Confirm the deletion in the popup prompt.
- To prevent the extension from returning, click your profile picture in the top right corner, select “Sync is on”, and click “Turn off” to temporarily disable extension syncing.
Microsoft Edge:
- In the “Manage extensions” menu, find the unwanted program.
- Click the “Remove” text located under the extension description.
- Click “Remove” again in the confirmation box.
- Click your profile icon, select “Manage profile settings”, click “Sync”, and temporarily turn off the “Extensions” toggle to prevent redownloading.
Apple Safari:
- In the “Extensions” settings tab, uncheck the box next to the suspicious extension’s name to disable it.
- With the extension highlighted, click the “Uninstall” button in the main window.
- If the extension is bundled with a Mac application, Safari will display a prompt telling you to remove the underlying app.
- Click “Show in Finder”, right-click the highlighted application, and select “Move to Trash”.
Managing Hidden Background Apps
Some browser-based applications are permitted to run invisibly in the background. These hidden processes can continue altering your search preferences even after you have closed all active browser windows.
Google Chrome:
- Open your browser settings menu.
- Click the “System” tab located on the left sidebar.
- Look for the toggle switch labeled “Continue running background apps when Google Chrome is closed”.
- Switch this setting to the “Off” position to prevent invisible scripts from operating.
- Restart your computer.
Microsoft Edge:
- Open your browser settings menu.
- Click the “System and performance” tab on the left sidebar.
- Locate the “System” section at the top of the page.
- Turn off the toggle switch labeled “Continue running background extensions and apps when Microsoft Edge is closed”.
- Restart your computer.
Apple Safari:
- Safari relies on the macOS to manage background tasks. Open your “Applications” folder, go to “Utilities”, and open “Activity Monitor”.
- Type “Safari” into the search bar at the top right corner.
- Look for any unusual processes running alongside your normal Safari tabs.
- If you spot a suspicious script or background app, highlight it and click the “X” icon at the top of the window to force quit the process.
System-Wide Cleanup and Advanced Troubleshooting
If you have cleaned your browser but the Yahoo redirect persists, the malicious software is operating outside the browser itself. It has embedded itself into your operating system.
To completely eradicate the problem, you must target your computer’s installed applications, fix manipulated system shortcuts, and deploy specialized software designed to hunt down stubborn hidden files.
Uninstalling Unauthorized Programs
Browser hijackers often arrive as standalone applications running quietly in the background of your operating system. You need to identify and completely uninstall these hidden programs to stop them from rewriting your browser preferences.
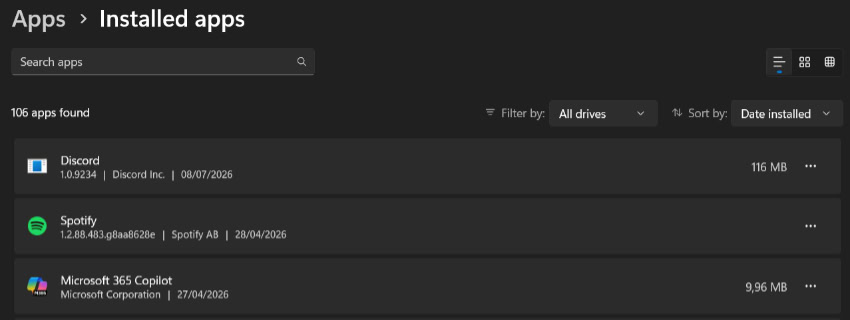
For Windows Users:
- Click the Start menu and type “Add or remove programs” into the search bar, then press Enter.
- Once the settings menu opens, locate the “Sort by” dropdown menu and change it to “Install date”.
- Scroll through the most recent installations and look for unfamiliar software. Pay close attention to programs with names containing words like “Search”, “Toolbar”, “Optimizer”, or “System Guardian”.
- Click on the suspicious application and select the “Uninstall” button.
- Follow the on-screen prompts to remove the software completely.
- Restart your computer to clear any lingering active processes from your system memory.
For Mac Users:
- Open a new Finder window.
- Click on “Applications” in the left sidebar.
- Click the “List” view icon at the top of the window, then click the “Date Added” column header to sort your applications by the most recent installations.
- Scan the list for unrecognized applications that you did not download yourself.
- Right-click the suspicious application and select “Move to Trash”.
- Right-click the Trash icon on your dock and select “Empty Trash” to permanently delete the program.
Checking Browser Shortcut “Target” Paths
A very common tactic used by hijackers is modifying the actual desktop or taskbar shortcut you use to launch your browser. They append a specific website address to the shortcut’s code, forcing the browser to load a malicious page or Yahoo redirect immediately upon opening.
- Locate the shortcut icon you normally use to open your browser on your desktop.
- Right-click the icon and select “Properties” from the context menu.
- Ensure you are looking at the “Shortcut” tab.
- Locate the text box labeled “Target”. This box shows the file path to your browser application.
- Look at the very end of the text string. A clean browser path will end with the application file, such as chrome.exe” or firefox.exe”.
- If you see a website address appended after the quotation marks, highlight that specific URL and delete it. Do not delete the path to the actual browser application.
- Click “Apply”, then click “OK” to save your clean shortcut.
Running Specialized Malware Scans
Standard antivirus programs sometimes miss browser hijackers because these threats often fall into a grey area between nuisance software and destructive viruses. To hunt down these specific scripts, you should use a targeted utility like AdwCleaner by Malwarebytes.
This free, lightweight tool is specifically built to eradicate adware, unwanted toolbars, and hijacked search configurations.
- Navigate to the official Malwarebytes website and download the free AdwCleaner utility.
- Close all open browser windows and save any active work on your computer.
- Open the downloaded file to launch the application. The program is portable and does not require a traditional installation process.
- Click the “Scan Now” button on the main dashboard to initiate the system sweep.
- Wait for the scan to finish. The tool will quickly comb through your registry and file system to locate hidden Potentially Unwanted Programs (PUPs).
- Review the resulting list of detected threats, then click the “Quarantine” or “Clean & Repair” button to neutralize them.
- Allow the application to restart your computer. This final step clears the malicious software from your active memory and completely severs its connection to your browser.
Proactive Prevention and Security Hygiene

Removing a browser hijacker solves the immediate problem, but keeping your machine clean requires a shift in your daily downloading habits. By understanding how deceptive software targets users and maintaining strict control over your system updates, you can easily prevent future unauthorized modifications to your search engine.
The “Custom Installation” Rule
The vast majority of browser hijackers are bundled directly into the installation files of legitimate freeware. When you run an installer, developers often offer an “Express” or “Recommended” installation path.
You should always refuse this option. The express route automatically grants the installer permission to add every bundled toolbar, search protector, and background application included in the package.
Always select the “Custom” or “Advanced” installation option. This manual route allows you to review a detailed list of every component being installed.
From there, you can manually uncheck the boxes next to any third-party software or search engine modifications before the installation begins.
Recognizing Dark Patterns
Software developers frequently use deceptive user interface designs, known as dark patterns, to trick you into accepting bundled software. As you click through an installation wizard, pay close attention to the layout of the buttons.
The setup wizard might present a page asking you to accept a search engine change, highlighting the “Accept” button in a bright, inviting color while making the “Decline” or “Skip” button incredibly small or faded. In some cases, the text will use confusing double negatives to ensure that clicking “No” actually means you agree to the installation.
Read every screen of a setup wizard carefully, read the fine print, and never rapidly click the “Next” button.
Maintaining Browser Health
A healthy browser is inherently more resistant to external manipulation. Outdated software frequently contains unpatched vulnerabilities that malicious scripts exploit to change your settings.
You must ensure your browser is set to update automatically. Check your settings periodically to verify that you are running the most recent version available.
Additionally, you should audit your browser extensions and computer applications every few months. Delete any tools or add-ons you no longer actively use.
Fewer installed applications mean fewer opportunities for unwanted software to hide or quietly update itself into a browser hijacker.
Conclusion
A stubborn Yahoo redirect is frustrating, but it is ultimately a solvable problem. By manually resetting your browser preferences, auditing your active extensions, and performing a thorough system-wide cleanup, you can effectively flush out the hidden scripts causing the interference.
Following these specific steps ensures you permanently restore control over your computer and reclaim your preferred browsing environment for good.
Frequently Asked Questions
Why does my browser keep redirecting to Yahoo?
Your browser is likely infected with a hijacker or a potentially unwanted program. These malicious scripts forcefully manipulate your internal configuration to route all web traffic through Yahoo. Developers do this to generate illicit advertising revenue from your daily internet searches.
Is the Yahoo search redirect a computer virus?
It is not a traditional virus, but it is classified as malicious software or malware. While it might not steal your passwords or corrupt your hard drive, it actively overrides your system commands and tracks your browsing habits without permission.
How do I stop Yahoo from taking over Chrome?
You must manually remove Yahoo from your managed search engines and restore Chrome to its default state. After clearing the corrupted internal configuration, immediately check your extension manager to permanently delete any unfamiliar add-ons that are forcing the unwanted redirect.
Can legitimate software change my default search engine?
Yes, many trusted antivirus programs and system optimization utilities frequently include proprietary web protection tools. These security suites will sometimes alter your preferences to explicitly route your queries through their partnered search providers in an attempt to filter out dangerous websites.
Why did the hijacker survive my browser reset?
If the unwanted redirect immediately returns after a complete reset, the malicious software is hiding deep inside your operating system. You must uninstall recently added desktop applications, fix modified shortcut paths, and run a dedicated antimalware scan to isolate the infection.


