Tor vs. VPN: Stop Using the Wrong Security App

Reclaiming your online privacy starts with choosing the right armor. As corporate data tracking and government surveillance grow more aggressive, everyday users often scramble to lock down their devices, resulting in widespread confusion over the available security tools.
The most frequent debate pits the Tor network directly against Virtual Private Networks (VPNs). People constantly argue over which option offers superior protection, yet this comparison misses the point entirely.
These two systems were built to defeat fundamentally different threats. To resolve this dilemma, we must decode the technical mechanics behind both systems, evaluate their fundamental differences, and highlight their specific real-world applications.
The Tor Network: Mechanics of Decentralized Anonymity
The Tor project offers a distinct approach to internet security by utilizing a global network of volunteers. Instead of routing traffic through a single corporate server, it relies on a complex web of decentralized nodes to obscure user activity.
This structure fundamentally changes how data travels across the internet to prioritize absolute user safety.
The Concept of Onion Routing
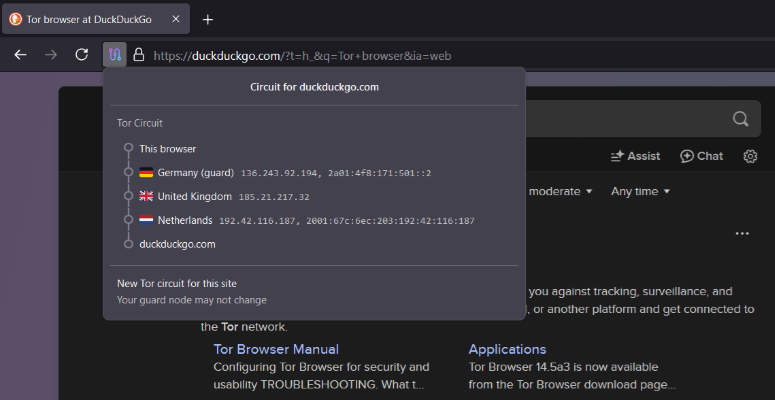
When you open the Tor Browser, your request does not travel straight to a website. The software instead creates a randomized path through three separate volunteer-operated servers.
These servers are designated as the Entry node, the Relay node, and the Exit node. Your internet traffic bounces randomly between these global points before finally reaching its intended destination.
This scattered routing process makes it virtually impossible for an outside observer to track the physical origin of the data request.
Multi-Layered Encryption
As your data prepares to leave your device, the Tor Browser encrypts it multiple times. Each layer of encryption corresponds to one of the specific nodes on your randomized path.
The Entry node peels away the first layer of encryption, revealing only the IP address of the next Relay node. The Relay node then peels away the second layer, sending the traffic forward to the Exit node.
Finally, the Exit node decrypts the last layer and delivers the raw data to the website. Because of this highly structured sequence, no single server in the chain ever possesses both your original identity and the final destination of your data.
Prioritizing Anonymity Over Privacy
The ultimate objective of the Tor network is strict anonymity. It specifically focuses on hiding exactly who you are from the websites you visit and the network administrators monitoring your local connection.
While standard encryption protects the contents of your data payload, Tor goes a step further by ensuring the sender remains completely untraceable. A malicious actor monitoring the exit node might be able to see the final data request, but they cannot trace that particular request back to your physical device or your home IP address.
Inherent Technical Limitations
The reality of bouncing encrypted traffic across randomly selected servers located around the globe creates massive performance bottlenecks. Connection speeds drop significantly compared to standard browsing, making heavy downloads entirely impractical.
Furthermore, because exit nodes are publicly known and shared by thousands of anonymous users, many commercial websites automatically flag this traffic as suspicious. Tor users frequently encounter endless CAPTCHA challenges, restricted access to basic web services, and outright bans on certain commercial platforms.
Virtual Private Networks: Mechanics of Centralized Privacy

Virtual Private Networks offer a completely different technical approach designed for everyday internet security. Rather than utilizing a volunteer network, a VPN relies on centralized infrastructure owned and operated by a private company.
This model simplifies the routing process while providing robust data protection against local surveillance.
The Encrypted Tunnel
When you activate a VPN application, it establishes a direct and secure tunnel between your device and a single designated server. The software applies a heavy layer of encryption to all outgoing data before it even leaves your machine.
This completely prevents anyone sharing your local network from reading your traffic. Whether you are connected to a public Wi-Fi hotspot at a coffee shop or a home network monitored by your Internet Service Provider, the contents of your internet activity remain safely hidden inside this secure tunnel.
IP Address Masking
Beyond encrypting the data payload, a VPN also effectively conceals your physical location from the websites you visit. As your traffic travels through the encrypted tunnel and arrives at the private server, the system intercepts the connection.
It then substitutes your actual IP address with the IP address belonging to the VPN server. Any website you visit will only register the server location, keeping your true geographical location shielded from online trackers.
Prioritizing Privacy Over Anonymity
VPNs are optimized to provide practical privacy rather than absolute anonymity. They excel at hiding exactly what you are doing from local snoops, network administrators, and internet service providers.
However, the VPN provider itself retains full visibility over your connection. The company providing the service knows your real IP address, your billing information, and the websites you frequent.
You are effectively completely private from the outside world, but you are never anonymous to the company managing the servers.
The Limitation of Centralized Trust
Relying on a centralized corporate entity introduces a massive vulnerability based entirely on blind trust. You must implicitly believe the company honors its stated “no-logs” policy and deletes your browsing history as promised.
If the provider decides to quietly monitor your traffic, or if law enforcement forces the company to hand over its internal server records, your privacy vanishes instantly. Using a VPN essentially means shifting your trust away from your local internet provider and placing it squarely onto a private software company.
Head-to-Head Comparison

Deciding between these two tools requires examining how their fundamental architecture impacts daily use. Evaluating them side by side reveals distinct practical advantages and significant drawbacks that dictate their everyday viability.
Speed and Bandwidth
The multi-node routing system used by Tor inherently throttles connection speeds to an extreme degree. Sending heavy files, participating in video calls, or attempting to stream high-definition media over a decentralized volunteer network is wildly impractical.
Conversely, premium VPN providers invest heavily in massive server farms specifically optimized for high bandwidth. A quality VPN connection operates fast enough to easily support competitive online gaming, massive file torrents, and seamless 4K video streaming with virtually zero noticeable latency.
Scope of Device Protection
The level of data protection varies drastically depending on how the software executes on your machine. The Tor network typically operates strictly at the application level.
If you launch the Tor Browser, only the specific web traffic occurring inside that particular browser window receives multi-layered encryption. Meanwhile, a commercial VPN operates at the operating system level.
Once activated, the VPN automatically encrypts every single piece of data leaving your device. This wide net includes background software updates, desktop email clients, multiplayer video games, and all other installed internet browsers.
Cost and Accessibility
The Tor project is entirely free and open-source. Anyone with a basic internet connection can download the browser and immediately access the secure network without ever providing a credit card, an email address, or a billing name.
On the other hand, maintaining a high-speed, secure, and centralized global server network requires massive corporate capital. Reputable VPN providers always charge recurring monthly or annual subscription fees to maintain their infrastructure.
While supposedly free VPNs do exist on app stores, they almost always fund their operations by secretly logging and selling user data to third-party advertisers.
Differing Trust Models
The starkest contrast between the two systems lies in exactly who you must trust. Tor relies entirely on decentralized open-source math and the collective effort of thousands of global volunteers.
You do not have to place your faith in a single company because the multi-layered encryption physically ensures no single server can compromise your identity. A VPN requires total faith in a centralized corporation.
You are handing over money to a private business and trusting that their proprietary software, internal security practices, and corporate integrity are completely uncompromised.
When to Use Which Tool
Evaluating your personal security needs is a crucial step before selecting a protective tool. This process involves determining exactly what data needs protection and who might be trying to access it.
A casual web surfer trying to watch a restricted movie requires vastly different security measures compared to a journalist communicating with a confidential source.
Scenarios for Using a VPN
VPNs provide excellent security for everyday privacy concerns. They are ideal for securing sensitive data while connected to unsecured public Wi-Fi networks at cafes, hotels, or airports.
Because the encryption tunnel shields your activity from local network snoops, you can safely log into bank accounts or send private emails. Furthermore, VPNs excel at bypassing geographic content restrictions.
By routing your connection through a server in another country, you can access streaming libraries or online games that are otherwise blocked in your physical location. Finally, leaving a VPN running in the background constantly prevents local internet service providers from tracking your daily browsing habits and selling that data to third-party marketing agencies.
Scenarios for Using Tor
The Tor network is designed for high-stakes anonymity where personal safety is on the line. Journalists, political dissidents, and whistleblowers operating in oppressive regimes rely on this decentralized routing to bypass severe censorship and communicate without being identified.
It is highly effective for evading state-level surveillance or highly targeted tracking efforts that would easily compromise a standard connection. Additionally, Tor is the safe way to access hidden .onion services hosted on the dark web.
Because these specific websites do not exist on the standard internet, the Tor Browser is required to reach them while maintaining the absolute anonymity of both the host and the visitor.
Mismatched Use Cases
Applying the wrong tool to a specific problem can completely undermine your security and disrupt internet infrastructure. Users should never use the Tor network for torrenting large files or streaming high-definition video.
The volunteer-operated nodes possess limited bandwidth, and forcing heavy media traffic through the network degrades connection speeds for individuals who genuinely need it to survive oppressive regimes. Conversely, high-risk activists and whistleblowers should never rely solely on commercial VPNs to hide their identities from powerful governments.
If a state intelligence agency pressures a corporate VPN provider, the company might surrender user logs or real-time connection data, instantly compromising the activist.
Advanced Security: Combining Both Tools
For users facing extremely sophisticated tracking methods, standard security protocols might not feel sufficient. It is technically possible to stack these two protective measures to leverage the distinct advantages of both systems simultaneously.
However, doing so requires careful execution and creates immense performance sacrifices.
The Tor Over VPN Method
The most secure and widely recommended way to merge these tools is known as the Tor over VPN method. To achieve this setup, the user simply activates their VPN software first and establishes a secure tunnel to a centralized server.
Once that connection is fully active, the user launches the Tor Browser and routes their traffic through the decentralized nodes. On a technical level, the encrypted Tor traffic travels entirely inside the encrypted VPN tunnel until it reaches the VPN server.
From there, the data enters the Tor network and bounces through the entry, relay, and exit nodes.
The Benefits of Combining
Stacking these tools provides two massive security benefits. First, it completely hides your Tor network usage from your local internet service provider.
Many network administrators and government agencies actively flag individuals who connect to Tor, assuming they are engaging in suspicious behavior. By connecting to a VPN first, your internet provider only sees a standard stream of encrypted VPN traffic.
Second, this method hides your actual home IP address from the Tor entry node. If a malicious entity manages to compromise the entry node, they will only discover the IP address of your chosen VPN server, keeping your physical location completely safe.
The Drawbacks
The primary consequence of this combined security setup is an extreme reduction in connection speed. The Tor network already suffers from severe latency issues due to the process of routing traffic through three random global servers.
Forcing that data through an additional layer of VPN encryption and an extra server hop compounds the delay. Loading basic text websites becomes a slow process, while downloading media or engaging in real-time communication becomes completely impossible.
Why VPN Over Tor is Discouraged
Attempting the reverse configuration, connecting to the Tor network first and then routing a VPN tunnel through the exit node, is heavily discouraged by security professionals. Setting up VPN over Tor involves immense technical complexity and requires complicated manual configuration that is highly prone to user error.
More importantly, this setup introduces severe security risks. By placing the VPN after the Tor exit node, you expose your final decrypted web traffic directly to the corporate VPN provider.
This effectively destroys the total anonymity that the Tor network was built to provide, rendering the entire complex setup entirely useless.
Conclusion
In the end, deciding between these systems rests entirely on your daily habits and the specific risks you face. Virtual Private Networks are the superior choice for high-speed, everyday data privacy against local trackers and restrictive networks.
In contrast, the Tor network is an essential tool for individuals who require absolute, uncompromised anonymity. Before installing any software, you must carefully evaluate your personal threat model.
You need to determine exactly what sensitive data needs protecting and precisely who might be trying to intercept it. By defining those specific parameters, you ensure your private information remains completely secure against the right threats.
Frequently Asked Questions
Is it safe to use Tor for online banking?
Using Tor for online banking is generally discouraged. Financial institutions frequently flag or block traffic originating from known Tor exit nodes due to fraud concerns. A standard VPN provides a much smoother, secure connection for checking your personal bank accounts without triggering automated security lockouts.
Can I be tracked while using a VPN?
Yes, you can still be tracked while using a VPN if you log into personal accounts or accept website cookies. A VPN successfully hides your real IP address and encrypts your local connection. However, it cannot stop social media platforms or search engines from monitoring your specific actions.
Does a VPN hide my activity from my internet service provider?
A VPN completely shields your browsing activity from your internet service provider. Once the encrypted tunnel is active, your provider can only see that you are sending secure data to a remote server. They cannot view the specific websites you visit or the files you download.
Is downloading the Tor browser completely legal?
Downloading and using the Tor browser is entirely legal in most democratic countries. Millions of regular people use it daily to bypass censorship and protect their personal privacy. However, a few highly restrictive regimes do actively block the network and penalize citizens caught utilizing the software.
Should I leave my VPN turned on all the time?
Leaving your VPN active at all times provides the best continuous protection for your personal data. This habit ensures your background applications remain encrypted and prevents accidental data exposure on unsecured public Wi-Fi networks. You only need to disable it if a specific local application requires your actual location.


